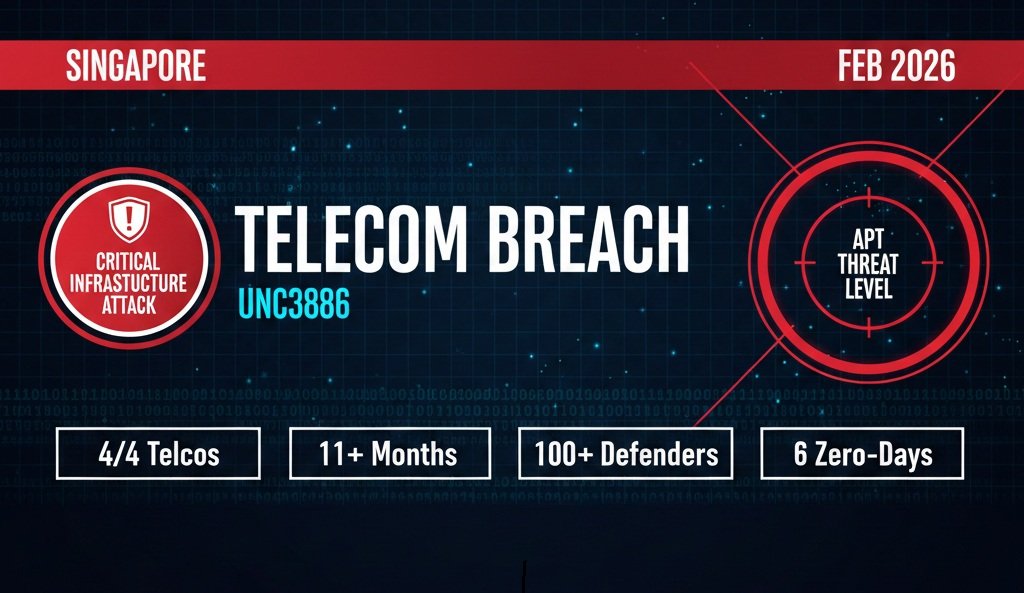
Singapore has confirmed that all four of its major telecommunications operators fell victim to a sophisticated cyber espionage campaign orchestrated by UNC3886, a China-linked advanced persistent threat (APT) group. The revelation, disclosed by Singapore’s Cyber Security Agency (CSA) on February 9, 2026, marks one of the most significant state-sponsored cyberattacks on critical infrastructure in Southeast Asia.
The targeted Singapore telecom operators M1, SIMBA Telecom, Singtel, and StarHub—represent the backbone of the nation’s digital infrastructure. In response, Singapore launched Operation CYBER GUARDIAN, its largest coordinated cyber incident response effort spanning more than eleven months, involving over 100 cyber defenders across multiple government agencies.
While authorities emphasize that the UNC3886 threat group did not succeed in exfiltrating customer data or disrupting telecommunications services, the campaign’s sophistication and strategic targeting raise critical questions about the vulnerability of critical telecom infrastructure worldwide.
Table of Contents
Understanding UNC3886: The China-Backed Cyber Espionage Powerhouse
UNC3886 represents one of the most technically proficient advanced persistent threat actors currently operating in the cyber espionage landscape. First identified by Google-owned Mandiant in 2022, this state-sponsored cyberattack group has consistently demonstrated an exceptional ability to exploit zero-day vulnerabilities and maintain undetected access to critical systems.
What Makes UNC3886 Different?
Unlike opportunistic cybercriminal groups, UNC3886 is described by security researchers as a “highly disciplined and stealthy” state-linked threat actor. The “UNC” designation indicates that while Mandiant has observed the group’s activities, it remains “uncategorized” pending definitive attribution to a specific nation-state entity. However, cybersecurity intelligence overwhelmingly links the group to Chinese state-sponsored cyber operations.
The China-backed hackers specialize in targeting strategic sectors including defense, telecommunications, finance, and critical infrastructure across the United States, Asia-Pacific, and Europe. Their operational focus on telecom sector cybersecurity makes them particularly dangerous, as telecommunications networks serve as critical conduits for vast amounts of sensitive data.
UNC3886’s Arsenal: Zero-Day Exploits and Custom Malware
The APT attack methods employed by UNC3886 represent the cutting edge of nation-state cyber capabilities. The group is known for using zero-day exploits and deploying custom open-source malware specifically developed to evade detection and maintain persistence within target networks.
Throughout 2024 and into 2025, UNC3886 exploited zero-day vulnerabilities in widely used technologies, including Fortinet FortiOS, VMware vCenter and ESXi hypervisors, and Juniper Networks systems. These critical vulnerabilities provided the foundation for the Singapore telecom cyberattack and similar campaigns worldwide.
Key exploited vulnerabilities include:
- CVE-2022-41328 (Fortinet FortiOS): Path traversal vulnerability enabling privileged file access
- CVE-2022-42475 (Fortinet FortiGate): Heap-based buffer overflow enabling code execution
- CVE-2022-22948 (VMware vCenter): Out-of-bounds write vulnerability enabling remote code execution
- CVE-2023-20867 (VMware Tools): Authentication bypass in VMware Tools
- CVE-2023-34048 (VMware vCenter): Out-of-bounds write enabling remote command execution
Organizations can verify patch status and remediation guidance through the National Vulnerability Database and CISA’s Known Exploited Vulnerabilities Catalog.
Advanced Malware Tools in the UNC3886 Toolkit
The sophistication of this cyber espionage operation extends beyond zero-day exploitation. UNC3886 deployed the REPTILE kernel-mode Linux rootkit, which provides stealthy process, file, and network hiding capabilities, as well as reverse shell access. Additionally, the MEDUSA rootkit, based on LD_PRELOAD techniques, was used for credential logging and command execution.
According to Trend Micro’s detailed analysis, the threat group’s custom malware arsenal includes:
- TINYSHELL: Covert remote access tool for command execution
- REPTILE: Stealthy Linux rootkit for process and file hiding
- MEDUSA: Credential harvesting and authentication logging rootkit
- VIRTUALSHINE: VMware VMCI sockets-based backdoor providing bash shell access
- VIRTUALPIE: Python backdoor supporting file transfer and command execution
- MOPSLED: Shellcode-based modular implant using GitHub for C2 communications
- RIFLESPINE: Cross-platform backdoor leveraging Google Drive for data exfiltration
- CASTLETAP: Passive backdoor for FortiGate firewalls triggered by ICMP packets
This diversified malware portfolio enables what cybersecurity experts call “layered persistence”—ensuring that even if defenders detect and remove one backdoor, alternative access channels remain available.
The Singapore Telecom Attack: Timeline and Tactics
The cyber espionage Singapore campaign against the nation’s telecommunications infrastructure represents a masterclass in patient, methodical infiltration of critical systems.
Detection and Initial Response
On July 18, 2025, Coordinating Minister for National Security K. Shanmugam publicly revealed that UNC3886 had been detected attacking Singapore’s critical infrastructure. However, no additional details were shared at that time to preserve operational security while cyber defenders worked to contain the threat.
The attacks were first detected when the telecommunications operators identified suspicious network activity and immediately alerted the Infocomm Media Development Authority (IMDA) and the Cyber Security Agency of Singapore (CSA), demonstrating the critical importance of robust threat monitoring in telecom network security.
Operation CYBER GUARDIAN: Singapore’s Multi-Agency Response
Over 100 cyber defenders across agencies including CSA, IMDA, the Centre for Strategic Infocomm Technologies (CSIT), the Digital and Intelligence Service (DIS), the Government Technology Agency of Singapore (GovTech), and the Internal Security Department (ISD) were involved in the operation.
This unprecedented coordination reflects Singapore’s mature approach to critical infrastructure protection and serves as a model for how nations should respond to state-sponsored attacks on essential services. The operation spanned eleven months, from mid-2025 through early 2026, representing Singapore’s largest and longest-running anti-cyber threat law enforcement operation.
Attack Methodology and Impact Assessment
In one instance, the hacking group used a zero-day exploit to bypass a perimeter firewall installed at the target companies and gained access into one of the victims’ networks. The attackers demonstrated sophisticated operational security by exfiltrating a small amount of technical data, likely network-related data to advance the threat actors’ operational objectives.
In another documented instance, UNC3886 deployed rootkits to establish persistent access and conceal their tracks to fly under the radar. This made detection extraordinarily challenging, requiring cyber defenders to conduct comprehensive security checks across the networks.
Critically, the threat actor was able to gain unauthorized access into some parts of telco networks and systems, with limited access to critical systems, but did not get far enough to disrupt services. Furthermore, there is no evidence that sensitive or personal data such as customer records were accessed or exfiltrated, and no evidence that the threat actor managed to disrupt telecommunications services.
Why Telecommunications Are Prime Targets for APT Groups
The targeting of Singapore’s telecommunications sector by this China-linked APT group is not coincidental. Telecommunications infrastructure represents a strategic prize for state-sponsored cyber espionage for several compelling reasons.
The Strategic Value of Telecom Infrastructure
Telcos play a foundational role in powering the digital economy and transmit vast amounts of information, including sensitive data. Access to telecommunications networks can potentially enable:
- Mass surveillance capabilities: Intercepting voice, text, and data communications
- Strategic intelligence gathering: Monitoring government and business communications
- Supply chain compromise: Using telecom infrastructure as a pivot point to reach customers
- Preparatory positioning: Establishing access for potential future disruption operations
According to CSA’s official statement, if threat actors succeed in attacking telcos, they have the potential to undermine national security and the economy.
Comparison to Other Telecom Cyber Espionage Campaigns
The UNC3886 Singapore campaign bears operational similarities to, but remains distinct from, the Salt Typhoon attacks that compromised hundreds of telecommunications companies globally. Singapore said the attack carried out by UNC3886 has “not resulted in the same extent of damage as cyberattacks elsewhere,” referring to the Salt Typhoon hacks.
The Salt Typhoon campaign, also attributed to Chinese state-sponsored actors, successfully compromised major U.S. and Canadian telecommunications providers, demonstrating a coordinated global strategy targeting critical telecommunications infrastructure. For more context on telecom-focused cyber espionage, consult TechCrunch’s coverage and The Record’s reporting.
Defense Strategies: Protecting Against Advanced Persistent Threats
The UNC3886 campaign provides critical lessons for organizations operating critical infrastructure, particularly in the telecommunications, defense, technology, and finance sectors.
Immediate Technical Mitigations
Organizations must take urgent action to address the specific vulnerabilities exploited in the Singapore telecom cyberattack:
- Apply Critical Patches Immediately: Prioritize patching CVE-2022-41328, CVE-2022-42475, CVE-2022-22948, CVE-2023-20867, and CVE-2023-34048 across all Fortinet, VMware, and Juniper systems.
- Implement Immutable Logging: UNC3886 is known for exploiting zero-day vulnerabilities in routers, firewalls, and virtualized environments, where cybersecurity tools designed to spot malware cannot typically reach. Deploy logging solutions that cannot be tampered with or deleted by attackers.
- Strengthen Virtualization Security: Given UNC3886’s focus on VMware environments, implement VMware’s hardening guides and ensure hypervisors are isolated from general network access.
- Deploy Network Segmentation: Limit lateral movement capabilities by implementing robust network segmentation between critical and non-critical systems.
Advanced Detection and Monitoring
The stealthy nature of UNC3886 operations demands enhanced detection capabilities:
- Behavioral Analytics: Deploy endpoint detection and response (EDR) solutions capable of identifying anomalous behavior patterns rather than relying solely on signature-based detection.
- Threat Hunting Programs: Establish proactive threat hunting teams that search for indicators of compromise (IOCs) associated with UNC3886 tactics, techniques, and procedures (TTPs). The MITRE ATT&CK framework provides detailed mappings of UNC3886 techniques.
- Virtualization-Specific Monitoring: Implement specialized monitoring for VMware vCenter, ESXi, and virtual machine activities to detect unauthorized guest operations and unusual administrative actions.
- Network Device Auditing: Regularly audit router, firewall, and network appliance configurations for unauthorized changes, backdoors, or suspicious processes.
Organizational and Strategic Defenses
Technical controls alone cannot defend against state-sponsored cyberattack capabilities. Organizations must adopt comprehensive security postures:
Zero Trust Architecture: Implement zero-trust security principles that verify every access request regardless of source location. The NIST Zero Trust Architecture provides implementation guidance.
Threat Intelligence Sharing: Participate in industry-specific Information Sharing and Analysis Centers (ISACs) to receive early warning of emerging threats. For telecommunications operators, the Communications ISAC provides sector-specific intelligence.
Incident Response Planning: Develop and regularly test incident response plans specifically designed for APT scenarios. The SANS Incident Response framework offers practical templates.
Supply Chain Security: Conduct thorough security assessments of third-party vendors and service providers who have access to critical systems.
Government Response and Policy Implications
Singapore’s response to the UNC3886 threat demonstrates a sophisticated understanding of modern cyber threats and the necessity of coordinated national-level responses.
Singapore’s Cybersecurity Posture
Minister for Digital Development and Information Josephine Teo emphasized the severity of the threat in remarks following the disclosure. She stressed that the cyberattack in Singapore highlighted the presence of persistent threat actors capable of targeting critical infrastructure, adding that sectors such as power, water, and transport could also face similar threats.
The minister’s statement underscores a critical reality: “Even as we try our best to prevent and detect cyber-attacks, we may not always be able to stop them in time. All of us must also be prepared for the threat of disruption.”
This acknowledgment of the limitations inherent in cyber defense, even with significant resources and expertise, represents a mature and realistic approach to cybersecurity resilience.
Ongoing Vigilance and Future Preparedness
CSA and IMDA have been working closely with telcos to strengthen their cyber defenses, enhance detection capabilities, and deploy active monitoring systems to maintain vigilance against new attempts by UNC3886 to re-enter their networks.
The comprehensive response includes:
- Joint threat hunting exercises between government and private sector
- Penetration testing of critical infrastructure
- Capability development programs for cybersecurity professionals
- Progressive introduction of enhanced security requirements for critical infrastructure operators
For organizations seeking to enhance their cybersecurity capabilities, Singapore’s Cyber Security Agency provides extensive resources and frameworks.
International Context and Attribution
While Singapore’s official statements carefully avoid direct attribution to the Chinese government, the international cybersecurity community has established clear links between UNC3886 and Chinese state-sponsored operations.
The Attribution Challenge
Google-owned cybersecurity unit Mandiant previously linked UNC3886 as an espionage group likely working on behalf of China. The technical evidence supporting this assessment includes:
- Tool overlap with known Chinese APT groups
- Targeting priorities aligned with Chinese strategic interests
- Operational patterns consistent with Chinese cyber espionage doctrine
- Technical infrastructure connections to Chinese networks
However, direct attribution of cyberattacks to specific nation-states remains politically sensitive. Singapore’s authorities haven’t publicly named any country behind the group, though some external security firms link UNC3886 to state actors.
Global Implications for Critical Infrastructure
The UNC3886 campaign against Singapore exists within a broader context of Chinese cyber operations targeting critical infrastructure worldwide. The Chinese government is known to conduct regular cyber-espionage operations, as well as prepositioning for disruptive attacks.
Similar campaigns targeting telecommunications and critical infrastructure have been documented across North America, Europe, and the Asia-Pacific region, suggesting a coordinated strategic approach to gaining access to global telecommunications networks.
Organizations should consult CISA’s alerts on PRC state-sponsored cyber activity for comprehensive threat intelligence.
Lessons Learned and Best Practices
The UNC3886 Singapore telecom cyberattack offers critical insights for defenders across all sectors.
Key Takeaways for Critical Infrastructure Operators
- Assume Persistent Threats: State-sponsored actors have the resources and motivation to maintain persistent presence in target networks for extended periods. Design security architecture accordingly.
- Prioritize Edge and Virtualization Security: UNC3886 is known for exploiting zero-day vulnerabilities in routers, firewalls, and virtualized environments, where cybersecurity tools that are designed to spot malware cannot typically reach. These blind spots require specialized security controls.
- Implement Defense in Depth: No single security control is sufficient. Layered defenses across network, endpoint, application, and data levels provide resilience even when individual controls fail.
- Foster Public-Private Collaboration: The success of Operation CYBER GUARDIAN demonstrates the power of coordinated response between government agencies and private sector operators.
- Maintain Operational Security: Singapore’s initial decision to withhold details about the attack to preserve operational security enabled defenders to work effectively without alerting attackers to detection.
Industry-Specific Recommendations
For Telecommunications Operators:
- Implement specialized monitoring for SS7, Diameter, and VoIP protocols
- Deploy telecom-specific threat intelligence feeds
- Conduct regular security assessments of interconnection points
- Establish incident response protocols for telecom-specific scenarios
For Virtualization Environments:
- Harden VMware vCenter and ESXi hypervisors according to vendor guidance
- Implement virtualization-aware security tools
- Restrict administrative access to virtualization management platforms
- Monitor for unauthorized guest operations and snapshots
For Network Device Security:
- Maintain comprehensive inventories of all network devices
- Implement out-of-band management networks for critical infrastructure
- Deploy network access control (NAC) solutions
- Regularly audit device configurations for unauthorized changes
Conclusion: The Evolving Landscape of State-Sponsored Cyber Threats
The UNC3886 campaign against Singapore’s telecommunications sector represents a sobering reminder that critical infrastructure faces persistent, sophisticated threats from well-resourced state-sponsored actors. While Singapore’s coordinated response through Operation CYBER GUARDIAN successfully limited the damage and contained the threat, the campaign demonstrates the evolving capabilities of advanced persistent threat groups.
The China-linked APT group’s use of multiple zero-day exploits, custom malware, and advanced evasion techniques sets a high bar for defenders. Organizations operating critical infrastructure must recognize that traditional security approaches are insufficient against this level of threat sophistication.
The path forward requires a fundamental shift in cybersecurity strategy—from reactive defense to proactive threat hunting, from isolated security to collaborative intelligence sharing, and from compliance-driven security to risk-based resilience. As Minister Josephine Teo acknowledged, we may not always prevent successful intrusions, but we must build the capability to detect, respond, and recover effectively.
The question is no longer whether your organization will face an advanced persistent threat, but whether you have the detection, response, and resilience capabilities to withstand one.












Leave a comment