Imagine waking up to find your critical business data—or even your personal files—locked away, inaccessible, with a chilling message demanding payment to get them back. This terrifying scenario is the reality of a ransomware attack, a form of cyber extortion that has become one of the most significant threats to individuals and organizations worldwide. In 2025, ransomware attacks continue to evolve, becoming more sophisticated and disruptive, making comprehensive ransomware protection and effective ransomware prevention more crucial than ever. Understanding how ransomware works, recognizing common ransomware attack vectors, and knowing how to implement a robust ransomware response plan are essential steps to safeguard against these pervasive cyber threats.
Table of Contents
Key Takeaways
- Ransomware is a digital kidnapping of your data. It encrypts your files or locks your system, demanding payment (ransom) for their release.
- Attack vectors are diverse. Phishing, unpatched systems, and compromised remote access are common entry points for ransomware.
- Prevention is paramount. Implement strong cybersecurity practices like MFA, regular backups, and Zero Trust principles to build enterprise ransomware security.
- A solid response plan is vital. Knowing what to do before an attack can minimize damage and speed up recovery.
- Paying the ransom is rarely recommended. It doesn’t guarantee data recovery and fuels future cyber extortion attacks.
What Is a Ransomware Attack?
At its core, a ransomware attack is a type of cyberattack where malicious software, known as ransomware, encrypts a victim’s files or locks their entire system, making it unusable. The attackers then demand a ransom—usually in cryptocurrency like Bitcoin, which is harder to trace—in exchange for a decryption key or access restoration. It’s akin to a digital hostage situation, where your valuable data is held captive.
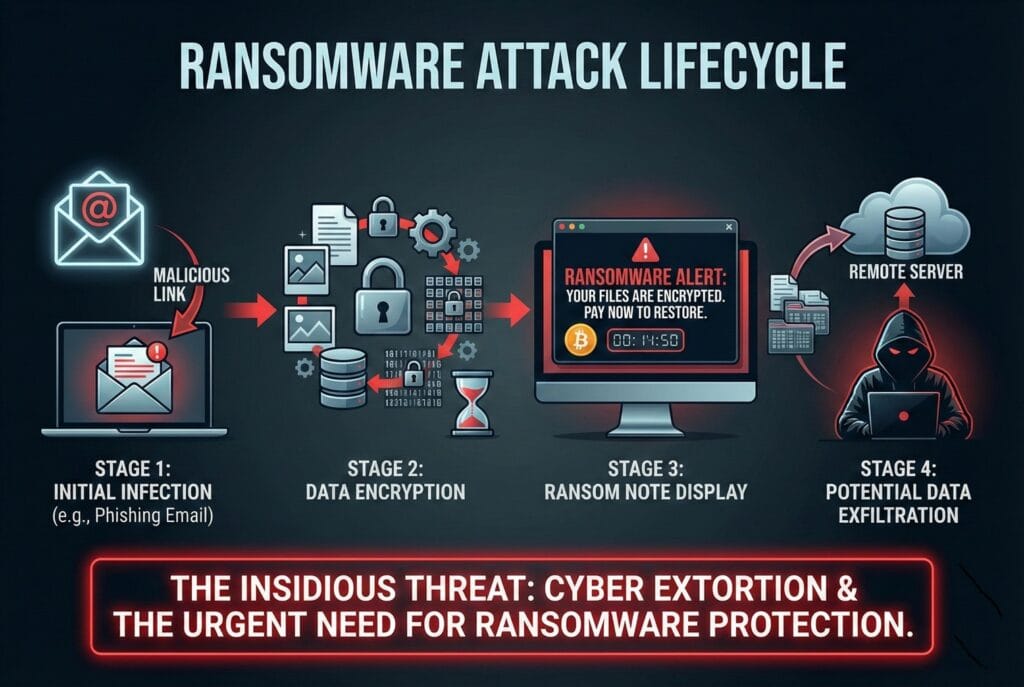
How Ransomware Works
The process typically begins with an initial infection. This could be through a malicious email attachment, a compromised website, or exploiting a vulnerability in your network. Once the ransomware gains a foothold, it silently spreads, identifying and encrypting files on the compromised system and often across connected networks. The encryption process uses strong algorithms, making it virtually impossible to decrypt the data without the unique key held by the attackers.
Encryption, Extortion, Double/Triple Extortion
Initially, ransomware focused on simple encryption and extortion: lock files, demand money. However, ransomware groups have evolved their tactics.
- Encryption: This is the foundational element. The ransomware employs sophisticated cryptographic algorithms to scramble files, rendering them unreadable and inaccessible without the correct decryption key.
- Extortion: After encryption, the attacker presents a ransom note, typically a text file or a full-screen message, detailing the demand, payment instructions, and a deadline. Failure to pay often results in the permanent loss of data or an increased ransom amount.
- Double Extortion: A significant evolution, double extortion attacks involve not only encrypting the victim’s data but also exfiltrating (stealing) it before encryption. The attackers then threaten to publish the stolen data if the ransom isn’t paid. This puts immense pressure on organizations, especially those dealing with sensitive customer or proprietary information, as it adds a data breach and reputational damage to the existing data loss.
- Triple Extortion: Taking it a step further, triple extortion adds another layer of pressure. Beyond data encryption and exfiltration, attackers might launch denial-of-service (DoS) attacks against the victim’s website or inform their customers, partners, or the media about the breach, amplifying the reputational and operational damage.
This constant evolution of tactics makes understanding how ransomware works critically important for anyone looking to bolster their enterprise ransomware security in 2025.
Common Ransomware Attack Vectors
Ransomware operators are constantly looking for new ways to infiltrate systems. Knowing these common entry points, or ransomware attack vectors, is the first step in effective ransomware prevention.
Phishing Emails & Malicious Attachments
This remains one of the most prevalent and effective methods. Attackers send carefully crafted phishing emails that appear legitimate, often impersonating trusted sources like banks, government agencies, or even internal IT departments. These emails typically contain malicious attachments (e.g., infected Word documents, PDFs, or executables disguised as invoices) or links to compromised websites. A single click by an unsuspecting employee can unleash ransomware into an entire network.
RDP & Remote Access Exploits
Remote Desktop Protocol (RDP) and other remote access services are legitimate tools for employees to work from home or for IT staff to manage systems remotely. However, if not properly secured with strong passwords and multi-factor authentication (MFA), RDP ports can become open doors for attackers. Ransomware groups actively scan the internet for weakly secured RDP connections to gain unauthorized access.
Unpatched Systems & Zero-Day Vulnerabilities
Software vulnerabilities are like weaknesses in a fortress wall. When software, operating systems, or network devices have known flaws that haven’t been patched, attackers can exploit these vulnerabilities to inject ransomware. Zero-day vulnerabilities are even more dangerous; these are flaws that are unknown to the software vendor (and thus unpatched) until they are actively exploited by attackers. Keeping all systems, applications, and firmware updated is a fundamental aspect of ransomware protection. You can learn more about 10 Strategies to Strengthen Digital Security which includes patching.
Compromised VPN Credentials
Virtual Private Networks (VPNs) are crucial for secure remote access, but if the credentials used to access them are compromised (e.g., through phishing, brute-force attacks, or credential stuffing), attackers can bypass perimeter defenses. Once inside the network via a legitimate-looking VPN connection, they can easily deploy ransomware. Strong password policies and MFA for all VPN access are non-negotiable for enterprise ransomware security.
Supply Chain & Third-Party Breaches
Organizations often rely on a complex web of third-party vendors and suppliers for various services. If one of these vendors has weaker security protocols and gets breached, attackers can leverage that access to infiltrate their clients’ networks. This “supply chain attack” vector means that even if your own defenses are strong, you could still be vulnerable due to a partner’s security lapse. This highlights the need for robust vendor risk management as part of your overall ransomware prevention strategy.
Major Ransomware Types
The world of ransomware isn’t monolithic; it comprises various types, each with its own specific modus operandi. Understanding these classifications helps in developing targeted ransomware protection strategies.
Crypto ransomware
This is the most common and widely known type. Crypto ransomware encrypts files on a victim’s system, making them inaccessible. Think of famous examples like WannaCry and NotPetya (though NotPetya had destructive worm-like qualities beyond pure ransomware). The goal is purely financial: pay the ransom, and you might get your files back. The encryption used is often very strong, making decryption without the attacker’s key incredibly difficult, if not impossible.
Locker ransomware
Unlike crypto ransomware, locker ransomware doesn’t encrypt individual files. Instead, it locks the entire computer system, preventing users from accessing their operating system or any applications. A full-screen ransom note typically appears, completely blocking the desktop. While less common for enterprise attacks now, it was prevalent in earlier years and could be highly disruptive, particularly for individual users.
Double Extortion Ransomware
As discussed earlier, this is a dangerous evolution that has become a dominant trend among ransomware groups in 2025. Attackers don’t just encrypt your data; they also steal a copy. This means even if you have perfect backups, you still face the threat of your sensitive data being leaked, leading to massive reputational damage, regulatory fines, and loss of trust. This tactic significantly increases the pressure on victims to pay.
RaaS (Ransomware-as-a-Service)
RaaS platforms have democratized cyber extortion, lowering the barrier to entry for aspiring cybercriminals. In a RaaS model, a ransomware developer creates the malicious code and then leases it out to “affiliates” (other criminals) for a cut of any successful ransoms. This allows individuals with limited technical skills to launch sophisticated ransomware attacks, making the threat landscape broader and more active. Many prominent ransomware groups operate under a RaaS model, continually evolving the tools and tactics available. This ecosystem makes it harder to track and dismantle these criminal operations.
Most Active Ransomware Groups in 2025
Staying informed about the most active ransomware groups and their evolving tactics is crucial for effective enterprise ransomware security in 2025. These groups are agile, constantly adapting, and represent a significant threat.
LockBit variants
LockBit has consistently been one of the most prolific and dangerous ransomware groups, operating a highly effective RaaS model. Their variants, such as LockBit 3.0 (also known as LockBit Black), offer fast encryption, sophisticated evasion techniques, and a user-friendly panel for affiliates to manage their attacks. They are known for targeting large enterprises across various sectors globally and are often at the forefront of ransomware trends 2025, using double extortion tactics aggressively. Their operational resilience, despite law enforcement efforts, makes them a persistent concern.
BlackCat/ALPHV
BlackCat, also known as ALPHV, emerged as a major player and quickly gained notoriety for its advanced capabilities. It was one of the first ransomware groups to be written in Rust, a programming language known for its performance and security features, which makes its malware harder to detect and analyze. Like LockBit, BlackCat utilizes double extortion and has targeted critical infrastructure and large corporations. They are known for their professionalism in negotiations and their sophisticated infrastructure, making them a top-tier threat.
Clop
Clop ransomware has a history of exploiting zero-day vulnerabilities in popular file transfer applications and network devices to gain initial access. They are infamous for large-scale data exfiltration and subsequent double extortion. Clop has repeatedly demonstrated its ability to conduct massive breaches by leveraging specific software flaws, often impacting hundreds of organizations simultaneously. Their focus on pre-exfiltration before encryption highlights a significant shift in the cyber extortion landscape.
Play
Play ransomware is another aggressive group that has gained traction for its targeted attacks against government entities and critical infrastructure. They typically employ double extortion tactics, focusing on exfiltrating sensitive data before encrypting systems. Play ransomware groups are known for their meticulous reconnaissance and tailored attacks, making them particularly difficult to defend against without advanced threat detection and proactive intelligence.
Emerging Groups
The ransomware landscape is highly dynamic, with new groups constantly emerging, often evolving from defunct operations or new RaaS offerings. These new players frequently adopt the tactics of established groups, such as double extortion, and continuously seek new vulnerabilities and attack vectors. Staying ahead requires continuous threat intelligence and adaptability in your ransomware prevention strategies. Monitoring these emerging threats is a key component of robust enterprise ransomware security.
Warning Signs of a Ransomware Infection
Detecting a ransomware infection early can be the difference between a minor incident and a catastrophic data loss. While ransomware often tries to remain stealthy, there are several tell-tale warning signs that something is wrong.
Unusual File Extensions
One of the most immediate and obvious signs is seeing unfamiliar or strange file extensions appended to your files. For example, your document.docx might suddenly become document.docx.lockbit or document.docx.enc. This indicates that your files have been encrypted by ransomware. Regularly reviewing file directories and being alert to these changes is crucial.
System Slowdown
Ransomware activity, especially during the encryption process, can consume significant system resources (CPU, disk I/O). If your computer or server suddenly becomes unusually slow, unresponsive, or applications crash frequently, it could be a sign that ransomware is actively working in the background.
Disabled Security Tools
Many ransomware variants attempt to disable or bypass antivirus software, firewalls, and other security tools to ensure their execution. If your security software suddenly stops working, reports errors, or cannot be updated, it’s a major red flag that something malicious is interfering with your system’s defenses.
Ransom Note Messages
The most definitive sign, of course, is the appearance of a ransom note. This could be a text file on your desktop (e.g., READ_ME.txt), a change in your desktop wallpaper displaying the demand, or a full-screen pop-up message. These notes typically contain instructions on how to pay the ransom, deadlines, and threats of data deletion or leakage if demands are not met. This is the ultimate indication of a cyber extortion attack.
How to Prevent Ransomware Attacks
Prevention is always better than cure, especially when it comes to ransomware. A multi-layered approach to ransomware prevention and strong enterprise ransomware security is essential in 2025.
Zero Trust Security Framework
Embrace a Zero Trust Security Framework where no user or device is inherently trusted, regardless of whether they are inside or outside the network perimeter. Every access request is verified. This involves:
- Continuous verification: Always verify identities and device posture.
- Least privilege access: Grant users only the minimum access necessary to perform their job functions.
- Micro-segmentation: Divide your network into small, isolated segments to limit lateral movement if a breach occurs.
Regular Patching & Vulnerability Management
Keep all operating systems, applications, firmware, and network devices updated with the latest security patches. Ransomware frequently exploits known vulnerabilities. Implement a robust vulnerability management program to regularly scan for and remediate weaknesses in your infrastructure. This includes actively monitoring for zero-day threats and applying emergency patches when critical vulnerabilities are discovered.
MFA & Identity Protection
Multi-Factor Authentication (MFA) adds a crucial layer of security by requiring more than one method of verification to access accounts (e.g., a password plus a code from a mobile app). Implement MFA for all critical systems, remote access (RDP, VPNs), and cloud services. Strong password policies, regular password changes, and employee awareness training on credential theft are also vital for identity protection.
Network Segmentation
Divide your network into smaller, isolated segments. If ransomware infiltrates one segment, proper network segmentation can prevent it from spreading easily to other critical parts of your infrastructure. This limits the damage and makes containment much easier during a ransomware incident. Isolate sensitive data and critical systems in their own segments with strict access controls.
Secure Backups & Offline Storage
This is arguably the most critical ransomware protection measure. Regularly back up all critical data. Ensure these backups are:
- Isolated: Stored separately from the main network, ideally on offline media or in immutable cloud storage, so ransomware cannot reach and encrypt them.
- Encrypted: To protect data privacy and integrity.
- Tested: Regularly verify that backups are restorable and free from corruption.
- Versioned: Keep multiple versions of backups to recover from various points in time.
Having reliable, isolated backups can render a ransomware attack ineffective, as you won’t need to pay the ransom to recover your data.
How to Respond to a Ransomware Incident
Even with the best ransomware prevention, an attack can happen. Having a well-defined ransomware response plan is paramount to minimizing damage and recovering swiftly. Remember, time is of the essence. You can also explore Automated Cybersecurity Incident Response to learn how automation can help.
Immediate Containment Steps
- Isolate Infected Systems: Disconnect compromised computers and servers from the network immediately. This prevents the ransomware from spreading further. Unplug network cables, disable Wi-Fi, and remove infected devices from shared storage.
- Activate Incident Response Team: Assemble your dedicated incident response team, or engage external cybersecurity experts.
- Preserve Evidence: Do not wipe or restart infected systems carelessly. Digital forensics will be crucial. Take images of infected drives for later analysis.
- Power Down Non-Essential Systems: If you suspect widespread infection but haven’t fully identified all affected systems, power down non-essential servers and devices to prevent further encryption.
Forensic Investigation
A thorough forensic investigation is vital to understand the attack. This involves:
- Identifying the Attack Vector: How did the ransomware get in? (Phishing, RDP, vulnerability exploit, etc.) This helps patch the initial entry point.
- Determining the Scope: Which systems are affected? What data has been encrypted or exfiltrated?
- Analyzing the Ransomware: Identify the specific ransomware strain and its characteristics. This can inform recovery efforts and potential decryption tools.
- Evidence Collection: Document everything for potential law enforcement involvement or insurance claims. Learn more about how to prepare for a cyber attack for more detailed insights.
Communication & Legal Considerations
- Internal Communication: Keep employees informed, but avoid panic. Provide clear instructions and updates.
- External Communication: If customer data or sensitive information has been compromised, you may have legal and regulatory obligations to notify affected parties and regulatory bodies. Consult with legal counsel immediately to understand your obligations, especially regarding data privacy laws (e.g., GDPR, CCPA).
- Law Enforcement: Report the incident to relevant law enforcement agencies (e.g., FBI, local police cybercrime units). They may have resources or intelligence that can help.
- Cyber Insurance: If you have cyber insurance, notify your provider promptly. They can offer support with incident response, legal advice, and potential financial coverage. Learn more about Cyber Insurance for Companies: Protecting Your Business in 2025.
Restore & Recovery Process
Once containment and investigation are underway, focus on recovery:
- Clean Systems: Ensure all infected systems are thoroughly cleaned of ransomware and any backdoor access points left by attackers. This might involve re-imaging machines.
- Restore from Backups: Use your secure, tested backups to restore encrypted data. This is where robust backup strategies pay off immensely.
- Implement Enhanced Security: Address the vulnerabilities exploited by the attack. Strengthen your ransomware protection measures immediately (e.g., enable MFA, patch systems, improve network segmentation).
- Post-Incident Review: Conduct a thorough review of the incident to identify lessons learned and improve your future ransomware prevention and response capabilities.
Should You Pay the Ransom?
This is one of the toughest decisions an organization faces during a cyber extortion attack. While the immediate urge might be to pay to recover data quickly, the consensus among cybersecurity experts and law enforcement is generally no, you should not pay the ransom.
Risks & Consequences
- No Guarantee of Data Recovery: Paying does not guarantee that attackers will provide a working decryption key or that all your data will be recovered. They might provide a faulty key, only partially decrypt files, or simply disappear.
- Funding Criminal Enterprises: Every ransom paid fuels the ransomware ecosystem, encouraging more attacks and empowering ransomware groups with resources to develop more sophisticated tools.
- Becoming a Repeat Target: Organizations that pay the ransom are often flagged as “easy targets” and may be targeted again by the same or different ransomware groups.
- Data Still May Be Leaked: In double extortion attacks, even if you pay for decryption, attackers may still leak the stolen data, arguing the payment was only for the key.
- High Financial Cost: The ransom itself can be exorbitant, and the hidden costs of a ransomware attack (downtime, investigation, reputational damage) far exceed the ransom amount.
Legal Implications
In certain jurisdictions, paying a ransom may have legal implications, especially if the ransomware group is sanctioned by governments. Making payments to sanctioned entities could result in legal penalties for your organization. Always consult legal counsel before considering any payment.
Alternative Recovery Approaches
The primary and most reliable alternative is a robust, regularly tested backup and recovery strategy. If you have clean, offline backups, you can restore your systems without engaging with criminals. Additionally, some cybersecurity firms or law enforcement agencies occasionally release decryption tools for specific ransomware strains, though this is not always available or effective. Focus your resources on strengthening your ransomware prevention and building an impenetrable ransomware response plan, rather than banking on paying off criminals.
Final Recommendations for Businesses
The threat of ransomware attacks is not going away in 2025. It will continue to evolve, becoming more sophisticated and targeted. For businesses of all sizes, adopting a proactive, comprehensive strategy for enterprise ransomware security is no longer optional—it’s imperative.
Here are my final, actionable recommendations to fortify your defenses:
- Prioritize Employee Training: Your employees are your first line of defense. Conduct regular, engaging cybersecurity awareness training to educate them about phishing, suspicious links, and social engineering tactics. Make them part of your ransomware prevention solution.
- Implement Multi-Factor Authentication (MFA) Everywhere: For every system, service, and application that supports it, enable MFA. This single step can prevent a vast majority of unauthorized access attempts, even if passwords are stolen.
- Maintain Immutable, Offline Backups: This cannot be stressed enough. Ensure your critical data is backed up, stored offline or in immutable storage, and regularly tested for restorability. This is your ultimate safety net against cyber extortion attacks.
- Patch and Update Religiously: Establish a rigorous patching schedule for all software, operating systems, and network devices. Automate where possible. Vulnerability management is foundational to preventing ransomware attack vectors from being exploited.
- Adopt a Zero Trust Architecture: Move beyond perimeter-based security. Assume breaches are inevitable and verify every user, device, and application before granting access. Implement least privilege access.
- Implement Network Segmentation: Divide your network into isolated segments to contain the spread of ransomware and limit its lateral movement if an infection occurs.
- Develop and Practice an Incident Response Plan: Don’t wait for an attack to happen. Create a detailed ransomware response plan, assign roles and responsibilities, and conduct regular drills. Knowing what to do in the critical moments can save your business.
- Invest in Advanced Security Tools: Deploy endpoint detection and response (EDR), next-generation firewalls, intrusion detection/prevention systems (IDPS), and email security gateways. Consider AI-driven threat detection tools to identify anomalies faster.
- Conduct Regular Cyber Risk Assessments: Understand your vulnerabilities and the potential impact of a ransomware attack on your specific business. This helps prioritize your security investments. For more details, explore how to conduct a cyber risk assessment for your business.
- Consider Cyber Insurance: While not a replacement for strong security, cyber insurance can help mitigate the financial impact of a ransomware incident, covering aspects like incident response, legal fees, and business interruption.
By focusing on these areas, businesses can significantly reduce their risk of falling victim to ransomware attacks and build resilience against the evolving ransomware trends 2025. Remember, cybersecurity is an ongoing journey, not a destination.














Leave a comment