Home
DLP
DLP
Awareness
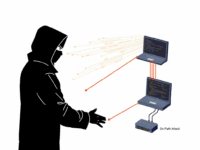
Data Loss Prevention (DLP) in 2025: How to Safeguard Your Sensitive Data
In today’s hyper-connected world, data isn’t just another business asset—it’s the bloodstream of the digital economy. And like blood, when it leaks, the...
ByKumar SJuly 3, 2025