How-To
Find practical how-to guides for cybersecurity tasks like setting up firewalls, checking compliances, securing cloud environments, and more. Follow simple steps to implement best practices, solve common issues, and strengthen your defenses with confidence.
Cybersecurity for Small Businesses: Why Small Businesses Are Prime Targets
In today’s digital age, cybersecurity for small businesses is no longer optional—it’s a necessity. Shockingly, 60% of small businesses close their doors within...
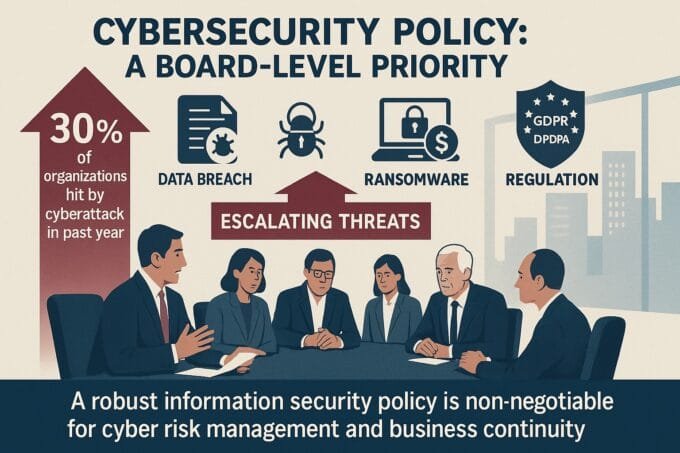
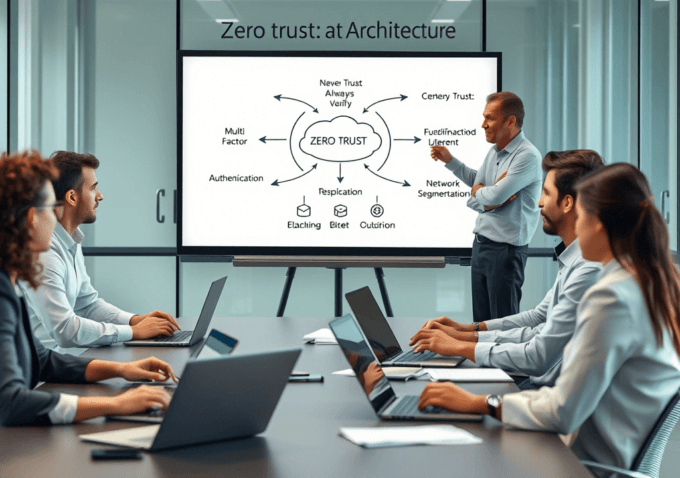
ByKumar SMarch 22, 2025How to Create a Robust Cybersecurity Policy for Your Organization
In 2025, the digital landscape is more interconnected and perilous than ever. Organizations face an unrelenting barrage of sophisticated cyberattacks, making a robust cybersecurity...
ByKumar SMarch 22, 2025How to Check If Your Data Was Exposed in the Latest Breach in 2025
The digital landscape in 2025 is more interconnected and vulnerable than ever before. With sophisticated cyberattacks becoming a daily occurrence, the question isn’t...
ByKumar SFebruary 19, 2025How to Prepare for a Cyber Attack: Essential Strategies for 2025
Did you know that cyberattacks occur every 39 seconds, affecting one in three Americans each year? That’s a staggering statistic that should make...
ByKumar SFebruary 14, 2025Cyber Awareness Challenge 2025 Answers : How to Protect Your Computers
Ever feel like our lives are practically glued to our screens these days? From online shopping to chatting with friends, managing our money,...
ByKumar SFebruary 5, 2025How to Protect SCADA Systems from Cyber Attacks: Best Practice
SCADA (Supervisory Control and Data Acquisition) systems control critical infrastructure, making them prime targets for cyberattacks. A breach can lead to catastrophic consequences,...
ByKumar SFebruary 5, 2025Enterprise AI Risk Management: How to Manage the Risk
As artificial intelligence becomes increasingly integrated into enterprise operations, organizations face a new landscape of security challenges that extend far beyond traditional cybersecurity...
ByKumar SFebruary 2, 2025