Home
Spam
Spam
Awareness
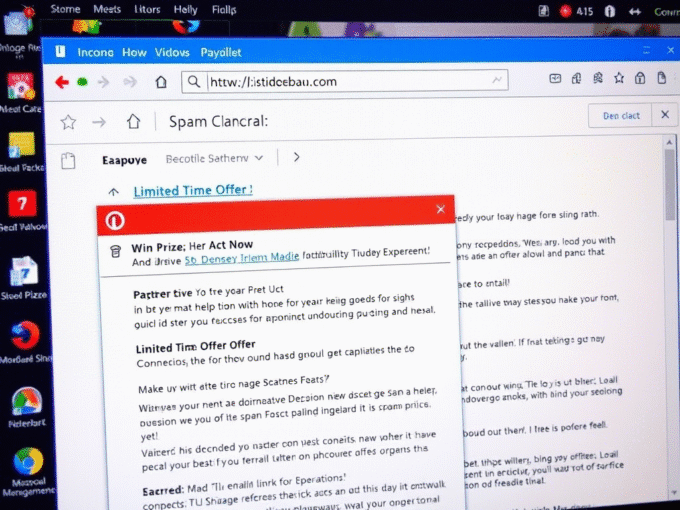
Inbox Overload? Sorting Through the Aggravation of Spam vs Phishing
Understanding the difference isn’t just about cleaning your inbox. Let's understand Spam vs Phishing
ByKumar SApril 25, 2025