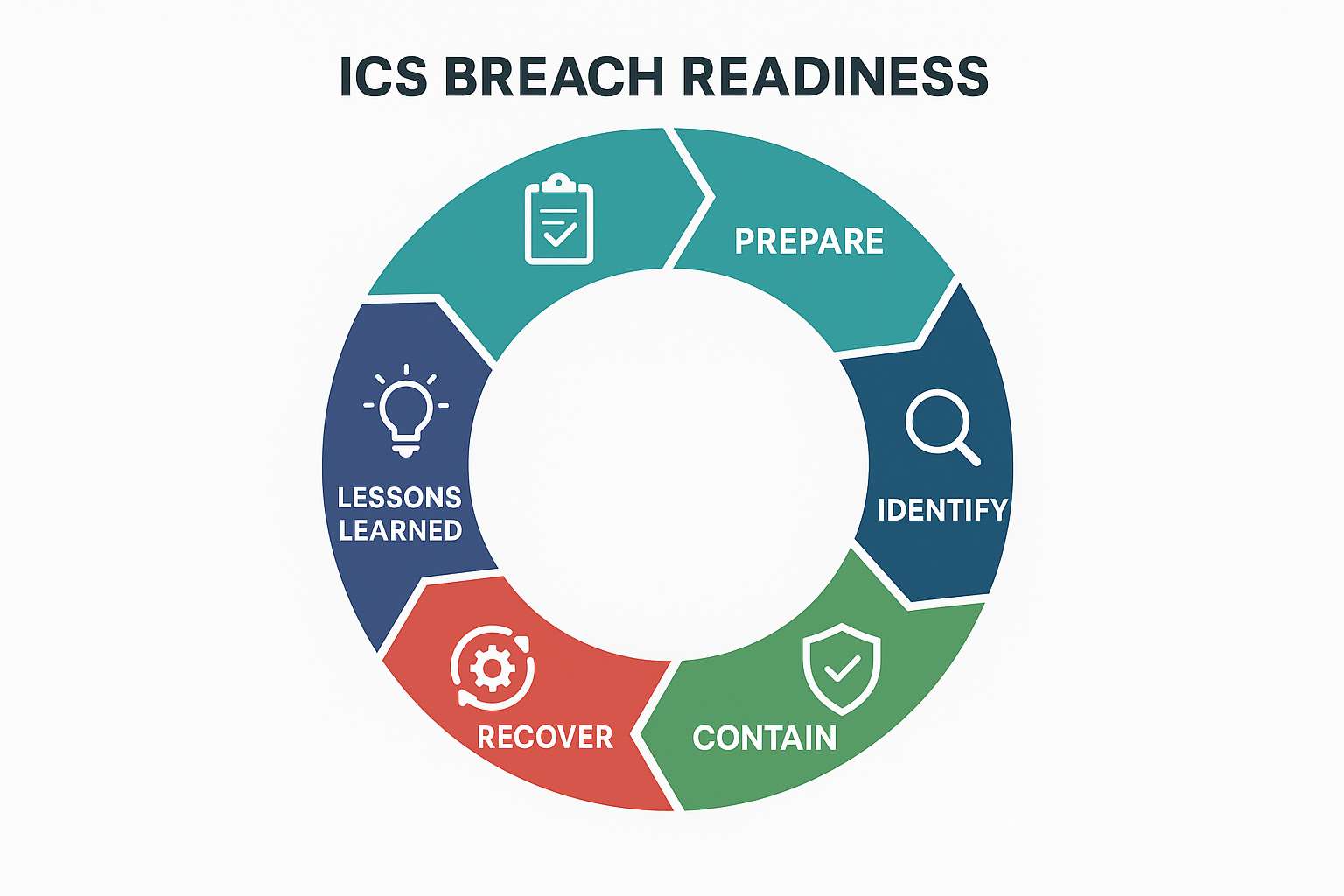
The digital landscape is constantly evolving, and with it, the threats to critical infrastructure grow more sophisticated. For organizations relying on Industrial Control Systems (ICS), a cybersecurity breach isn’t just a data theft concern; it can mean operational shutdown, environmental damage, or even loss of life. In 2025, understanding how to respond to an ICS cybersecurity breach is paramount for any industrial entity. This comprehensive guide will walk you through the essential steps for ICS breach response, from proactive readiness to robust ICS incident recovery and ongoing resilience. We’ll delve into the intricacies of industrial control systems security and outline critical OT ICS cyber incident recovery steps to ensure your operations can weather the storm.
Table of Contents
Key Takeaways
- Preparation is Non-Negotiable: A well-defined incident response plan, regular training, and robust security architecture are the bedrock of effective ICS breach response.
- Immediate Action is Crucial: Rapid detection, isolation of affected systems, and thorough damage assessment are vital in the initial moments of an ICS incident.
- Containment & Eradication: Strategic segmentation and meticulous threat removal are key to preventing lateral movement and complete system compromise.
- Structured Recovery: A phased approach to system restoration, validation, and vulnerability patching ensures operational integrity and prevents re-infection.
- Continuous Improvement: Post-incident analysis, updated playbooks, and ongoing security enhancements are essential for long-term industrial control systems security.
Understanding the Unique Challenges of ICS Cybersecurity Breaches
Responding to a cybersecurity breach in an Information Technology (IT) environment is inherently different from responding to one in an Operational Technology (OT) or ICS environment. Why? Because ICS/OT systems control physical processes – think power grids, water treatment plants, manufacturing lines, and transportation networks. The stakes are incredibly high.
Unlike IT systems, where the primary concerns are often data confidentiality and integrity, an ICS breach can impact:
- Safety: Malicious manipulation of control systems can lead to dangerous equipment malfunctions, explosions, or environmental releases.
- Availability: Downtime in critical infrastructure due to a cyberattack can have widespread societal and economic consequences.
- Integrity of Processes: Corrupted control commands or sensor data can cause production errors, quality issues, and equipment damage.
- Legacy Systems: Many ICS environments contain outdated hardware and software that are difficult to patch, integrate with modern security solutions, or even take offline for maintenance.
- Real-time Operations: The need for continuous operation often limits the ability to perform security scans or apply patches without disrupting critical processes.
- Interconnectivity: The increasing convergence of IT and OT networks, while beneficial for efficiency, also creates new attack vectors that threat actors are eager to exploit.
Given these unique characteristics, a specialized approach to ICS breach response is not just recommended, it’s absolutely essential. Effective industrial control systems security requires a deep understanding of both cyber principles and physical process controls. To further your understanding of the landscape, you might find our insights on cybersecurity in industrial control systems: best practices, threats in 2025 particularly useful.
Phase 1: Readiness – Preparing for an ICS Cybersecurity Incident
The most effective ICS incident recovery begins long before an actual breach occurs. Proactive preparation is the cornerstone of a resilient industrial control systems security posture.
A. Develop a Comprehensive ICS Incident Response Plan (IRP)
Your IRP is your playbook for a breach. It should be specifically tailored to your OT environment and outline clear, actionable steps. A robust IRP should include:
- Defined Roles and Responsibilities: Who does what during an incident? This includes internal teams (OT engineers, IT security, legal, communications) and external partners (law enforcement, cybersecurity vendors).
- Communication Protocols: How will information flow internally and externally? This includes executive leadership, employees, customers, regulators, and the public.
- Escalation Procedures: Clear thresholds for when an incident needs to be escalated to higher management or external authorities.
- Containment Strategies: Pre-approved methods for isolating compromised systems without causing further operational disruption.
- Recovery Procedures: Detailed steps for restoring systems, data, and operations.
- Legal and Regulatory Considerations: Understanding your obligations regarding data breach notifications, industry-specific regulations, and reporting requirements in 2025.
- Documentation Templates: Ready-to-use forms for logging incident details, actions taken, and lessons learned.
B. Conduct Regular Risk Assessments and Vulnerability Management
Understanding your attack surface is critical. Regularly assess your ICS environment for vulnerabilities, including:
- Network Architecture: Identify all connections between IT and OT networks, and ensure proper segmentation.
- System Inventories: Maintain an up-to-date list of all hardware, software, firmware, and network devices in your ICS environment.
- Configuration Management: Ensure all systems are securely configured and unnecessary services are disabled.
- Patch Management: Develop a strategy for patching vulnerabilities in ICS systems, recognizing the challenges of uptime and legacy hardware.
- Third-Party Risk: Evaluate the security posture of vendors and suppliers who have access to your ICS.
C. Implement Robust ICS Security Controls
A strong defense reduces the likelihood and impact of a breach. Key controls for industrial control systems security include:
- Network Segmentation: Isolate critical control systems from less secure networks and the internet. Use firewalls and VLANs to create secure zones.
- Strong Authentication: Implement multi-factor authentication (MFA) for all remote access and privileged user accounts.
- Access Control: Apply the principle of least privilege, ensuring users and systems only have the access they need to perform their functions.
- Anomaly Detection: Deploy Intrusion Detection Systems (IDS) and Security Information and Event Management (SIEM) tools specifically designed for OT environments to detect unusual activity.
- Endpoint Protection: Implement anti-malware and host-based intrusion prevention on all accessible endpoints within the ICS network where feasible.
- Backup and Recovery Solutions: Regularly back up critical ICS configurations, data, and software. Test these backups periodically to ensure they are recoverable.
- Physical Security: Control access to ICS equipment and control rooms to prevent unauthorized tampering.
D. Employee Training and Awareness
People are often the weakest link. Comprehensive training is essential for everyone, from operators to executives.
- Cybersecurity Awareness: Educate all employees about common cyber threats like phishing, social engineering, and the importance of strong passwords.
- Incident Response Drills: Conduct tabletop exercises and simulations of various ICS breach scenarios to test your IRP and train your team on how to respond to ICS cybersecurity breach.
- Role-Specific Training: Ensure OT engineers understand their role in securing the control systems and responding to incidents.
Phase 2: Response – Actions During an ICS Incident
When an incident occurs, time is of the essence. A structured approach can mitigate damage and accelerate ICS incident recovery.
A. Detection and Verification
The first step is to accurately detect and verify the presence of a breach. This is where your monitoring tools and vigilant staff come into play.
- Monitor Alarms and Anomalies: Pay close attention to unusual network traffic, system errors, unauthorized access attempts, or unexpected process changes. OT-specific monitoring solutions can be invaluable here.
- Initial Triage: Once an anomaly is detected, quickly determine if it’s a false positive or a genuine security incident. Involve both IT and OT experts in this assessment.
- Confirm the Breach: If initial triage suggests a breach, move quickly to confirm its nature and scope without causing further disruption. For insights on potential threats, consider reading about cyber threats 2024: key incidents and what to expect in 2025.
B. Identification and Assessment
Once a breach is confirmed, you need to understand its impact and characteristics.
- Identify Affected Systems: Pinpoint which ICS components (PLCs, RTUs, HMIs, SCADA servers, engineering workstations) have been compromised.
- Determine Attack Vector: How did the attacker gain entry? (e.g., phishing, unpatched vulnerability, remote access exploit, supply chain compromise).
- Assess Impact: Evaluate the extent of the damage. Is it just data exfiltration, system modification, or active process manipulation? What are the potential safety, environmental, and financial implications?
- Preserve Evidence: Crucially, begin collecting forensic data (logs, memory dumps, network captures) without altering the compromised systems if possible. This evidence is vital for understanding the attack and for any potential legal proceedings.
C. Containment
The goal of containment is to stop the spread of the attack and limit further damage. This requires careful coordination to avoid exacerbating the situation.
- Isolate Affected Systems: Disconnect compromised ICS components from the network. This might involve air-gapping, VLAN segmentation, or physically unplugging devices. Caution: Ensure isolation doesn’t cause instability or unsafe conditions for other operational systems. Manual control may be necessary.
- Block Malicious Traffic: Update firewalls and intrusion prevention systems to block known attacker IP addresses, domains, and malware signatures.
- Disable Compromised Accounts: Revoke credentials for any accounts suspected of being compromised.
- Implement Temporary Controls: Deploy immediate, temporary security measures to protect uncompromised systems.
This phase is critical for effective ICS breach response. For more detailed guidance on protecting control systems, refer to our article on how to protect SCADA systems from cyber attacks: best practice.
D. Eradication
Once contained, the next step is to remove the threat entirely from your environment.
- Remove Malware: Use forensic tools and antivirus solutions to identify and remove all traces of malware from affected systems. This might involve specialized OT-aware security tools.
- Eliminate Backdoors: Identify and close any backdoors or persistent access mechanisms established by the attacker.
- Patch Vulnerabilities: Address the root cause of the breach by applying necessary security patches, hardening configurations, and fixing architectural weaknesses.
- Rebuild or Restore: In severe cases, it might be necessary to completely rebuild compromised systems from trusted backups or golden images.
Phase 3: Recovery – Restoring Operations and Building Resilience
After eradication, the focus shifts to restoring normal operations securely and strengthening your defenses against future attacks. This is where the OT ICS cyber incident recovery steps truly shine.
A. System Restoration and Validation
Bringing systems back online requires meticulous planning and execution.
- Prioritize Recovery: Restore critical ICS systems first to minimize operational downtime and safety risks.
- Clean Room Recovery: If systems were heavily compromised, consider restoring them in an isolated “clean room” environment before reintroducing them to the production network.
- Validate Integrity: Thoroughly test restored systems to ensure they are functioning correctly and are free from malware or lingering vulnerabilities. This includes operational testing and security checks.
- Secure Reintegration: Carefully reintegrate systems into the ICS network, ensuring all new security controls and configurations are in place.
B. Post-Incident Activities
Recovery isn’t just about getting systems back online; it’s also about learning and improving.
- Forensic Analysis Completion: Continue deep forensic analysis to fully understand the attack, including the adversary’s techniques, tactics, and procedures (TTPs).
- Post-Mortem Analysis: Conduct a comprehensive review of the incident.
- What happened?
- How did we respond?
- What worked well?
- What didn’t work well?
- What could we do better next time?
- Document all findings in a formal report.
- Lessons Learned & Plan Updates: Use the insights from the post-mortem to update your ICS Incident Response Plan, security policies, and technical controls. This is vital for continuous improvement in industrial control systems security.
- Communication and Reporting: Fulfill all legal and regulatory notification requirements. Communicate transparently with stakeholders as appropriate.
- Strengthen Defenses: Implement long-term security enhancements identified during the recovery process. This might include investing in new security technologies, improving employee training, or revising architectural designs. Our article on automated cybersecurity incident response offers valuable insights for futureproofing your strategy.
Key Roles and Responsibilities in ICS Incident Response
Effective ICS breach response requires a multidisciplinary team. Here’s a look at some critical roles:
| Role | Key Responsibilities During an ICS Incident |
|---|---|
| CISO/Head of Security | Oversees the entire response, makes high-level decisions, manages external communications (with CEO/Legal), ensures resource allocation. |
| Incident Commander | Leads the tactical response, coordinates team efforts, ensures IRP adherence, provides updates to leadership. |
| OT Security Analyst/Engineer | Focuses on ICS-specific forensics, malware analysis, system isolation, and secure recovery within the OT network. Deep understanding of control systems is key. |
| IT Security Analyst/Engineer | Handles IT network forensics, threat intelligence, endpoint security in IT systems, and ensures IT/OT connectivity is secured. |
| Operations Team (OT Staff) | Provides critical process knowledge, assists with manual overrides, validates system functionality post-recovery, ensures safety. |
| Legal Counsel | Advises on legal obligations, regulatory compliance, data breach notification requirements, and potential liability. |
| Communications Team | Manages internal and external messaging, public relations, and stakeholder communications to maintain trust and control narratives. |
| Executive Leadership | Provides overall guidance, approves critical decisions (e.g., shutdowns, major investments), and supports the incident response team. |
Evolving Threats and Proactive Measures in 2025
The threat landscape for ICS environments is not static. In 2025, we continue to see:
- Ransomware-as-a-Service (RaaS): Increasingly targeting OT environments, often with devastating consequences. Proactive measures, including robust backups and air-gapped recovery strategies, are more critical than ever. Learn about essential steps for protection against ransomware in 2025.
- Supply Chain Attacks: Attackers compromise third-party vendors to gain access to target ICS networks. Thorough vendor risk management is paramount.
- Nation-State Actors: These sophisticated groups continue to target critical infrastructure for espionage, disruption, or sabotage. Their advanced persistent threat (APT) tactics require advanced detection capabilities.
- IT/OT Convergence Risks: As IT and OT networks become more integrated, the attack surface expands. Secure gateways and unidirectional data flows are crucial.
- AI-Enhanced Attacks: The use of Artificial Intelligence (AI) by adversaries for reconnaissance, vulnerability exploitation, and evasion is a growing concern. Conversely, AI can also bolster defenses, as explored in AI threat detection tools that actually work.
To stay ahead, organizations must continually invest in their industrial control systems security, conducting regular threat hunting, adopting a zero-trust model where feasible, and fostering a culture of cybersecurity awareness throughout the organization. Consider the benefits of ICS cyber resilience: building business continuity beyond firewalls to strengthen your defenses.
Bottom Line
Responding to an ICS cybersecurity breach is a complex, high-stakes endeavor that demands meticulous preparation, swift action, and continuous improvement. In 2025, no industrial organization can afford to be complacent about their industrial control systems security. By developing a comprehensive incident response plan, implementing robust security controls, regularly training personnel, and proactively adapting to evolving threats, you can significantly reduce your risk exposure and enhance your resilience.
The journey to effective ICS breach response and ICS incident recovery is ongoing. It requires a dedicated team, strong leadership, and a commitment to integrating security into every aspect of your OT operations. Remember, the goal isn’t just to react to a breach, but to build a robust security posture that can deter, detect, and swiftly recover from even the most sophisticated attacks, ensuring the safety and continuity of your critical industrial processes.
Actionable Next Steps:
- Review and Update Your IRP: Ensure your ICS Incident Response Plan is current, tested, and specifically addresses OT/ICS unique challenges.
- Conduct a Gap Analysis: Assess your current industrial control systems security posture against industry best practices and identify areas for improvement.
- Schedule a Tabletop Exercise: Simulate a realistic ICS breach scenario with your incident response team to identify weaknesses in your plan and train personnel.
- Invest in OT-Specific Security Solutions: Explore tools designed for ICS visibility, threat detection, and anomaly analysis.
- Foster IT/OT Collaboration: Ensure strong communication and collaboration between your IT and OT teams.













Leave a comment