Is the thought of a career in cybersecurity exciting but also a little overwhelming? You’re not alone! Many people feel that way when looking at the vast and rapidly evolving landscape of digital defense. But imagine having a clear, step-by-step guide to navigate this journey. That’s exactly what we’re here to provide. This comprehensive article will lay out your cybersecurity roadmap 2025, detailing every crucial step from being a complete beginner to becoming a seasoned professional. We’ll explore the diverse cybersecurity career path options available, ensuring you have the knowledge to make informed decisions and build a thriving future in this critical field.
Table of Contents
Key Takeaways
- Start with Fundamentals: A strong understanding of IT basics, networking, and operating systems is the bedrock of any cybersecurity career. Don’t skip these essential building blocks.
- Certifications are Your Allies: Industry-recognized certifications like CompTIA Security+, CEH, and CISSP are vital for validating your skills and opening doors to new opportunities.
- Specialization is Key for Growth: The cybersecurity field is vast. Identify areas like cloud security, incident response, or ethical hacking that align with your interests and specialize.
- Hands-on Experience is Non-Negotiable: Labs, CTFs (Capture The Flag), personal projects, and internships are crucial for turning theoretical knowledge into practical skills.
- Continuous Learning is a Must: Cybersecurity evolves daily. Embracing a mindset of lifelong learning and staying updated on the latest threats and technologies is paramount for long-term success.
Laying the Foundation: The Beginner’s Guide to the Cybersecurity Roadmap 2025

Embarking on a cybersecurity journey in 2025 means starting with a solid foundation. Think of it like building a house – you wouldn’t start with the roof, right? You need strong footings and a sturdy frame. The same goes for your cybersecurity career.
The good news is that cybersecurity is for anyone entering the digital defense frontier in 2025, regardless of your current technical background. While a degree in computer science or a related field can be helpful, it’s certainly not a strict requirement. Many successful cybersecurity professionals come from diverse backgrounds, having pivoted into the field through dedication and self-study.
The initial steps on your cybersecurity roadmap 2025 involve grasping fundamental concepts that underpin all digital systems.
Essential Core IT Skills for Aspiring Cyber Professionals
The initial steps on your cybersecurity roadmap 2025 involve grasping fundamental concepts that underpin all digital systems.
Essential Core IT Skills for Aspiring Cyber Professionals
Before you can defend networks, you need to understand how they work. Before you can protect data, you need to know how it’s stored and managed. Here’s a breakdown of the core IT skills you’ll need:
Networking Fundamentals (CompTIA Network+ level):
- TCP/IP: The language of the internet. Understanding how data packets travel is critical.
- OSI Model: A conceptual framework for understanding network communication.
- Network Devices: Routers, switches, firewalls – what they do and how they interact.
- Network Topologies: How networks are structured.
- Wireless Security: Wi-Fi standards and common vulnerabilities.
Operating Systems (OS) Knowledge (Windows, Linux, macOS):
- Command Line Interface (CLI): Especially for Linux (Bash) and Windows (PowerShell), this is your direct interface with the system.
- File Systems: How data is organized and stored.
- User Management: Permissions, groups, and access controls.
- System Hardening Basics: Initial steps to make an OS more secure.
Basic Programming/Scripting (Python, PowerShell):
- While you don’t need to be a full-stack developer, knowing how to read and write simple scripts is invaluable. Python is a top choice for automation, analysis, and security tools. PowerShell is critical for Windows environments.
Database Fundamentals:
- Understanding how databases store and manage information (SQL basics) is crucial, as many cyberattacks target data residing in databases.
Cloud Computing Basics:
- With more and more infrastructure moving to the cloud, a basic understanding of cloud service models (IaaS, PaaS, SaaS) and major providers (AWS, Azure, GCP) is essential. Explore cloud security best practices early on.
“The foundational knowledge is like a compass. Without it, you’re just wandering. With it, you can navigate any challenge.”
Foundational Certifications: Your First Steps on the Cybersecurity Career Path
Certifications validate your knowledge and show potential employers that you’re serious. For beginners, a few stand out:
- CompTIA A+: While not strictly cybersecurity, it covers PC hardware, software, networking, and troubleshooting. A great starting point if you’re entirely new to IT.
- CompTIA Network+: Focuses on networking concepts and infrastructure, which is a prerequisite for understanding network security.
- CompTIA Security+: This is often considered the entry-level benchmark for cybersecurity professionals. It covers core security functions, including threats, vulnerabilities, security architecture, identity management, and risk management. It’s a fantastic first step into a dedicated cybersecurity career path.
Table: Entry-Level Certifications Overview
| Certification | Focus Area | Target Audience | Prerequisite |
|---|---|---|---|
| CompTIA A+ | IT infrastructure, hardware, software | IT Support, Help Desk | None |
| CompTIA Network+ | Networking concepts, infrastructure | Network Admin, Support Specialist | A+ (recommended) |
| CompTIA Security+ | Core cybersecurity principles, risk management | Entry-Level Cybersecurity | Network+ (recommended) |
| (ISC)² CC | Foundational security principles | Entry-Level, Career Changers | None |
Advancing Your Cybersecurity Career Path: Intermediate Stages in 2025
Once you’ve mastered the basics, it’s time to deepen your knowledge and begin exploring specific areas of cybersecurity. This is where your cybersecurity roadmap 2025 starts to branch out, offering various exciting specializations.
Popular Cybersecurity Specializations for 2025
The field of cybersecurity is vast, and few professionals are experts in everything. Specializing allows you to develop deep expertise in a particular domain, making you a highly valuable asset.
- Network Security: Focuses on protecting network infrastructure and data in transit. This involves firewalls, intrusion detection/prevention systems (IDPS), VPNs, and secure network design. If you enjoy understanding network architecture, this might be for you. Learn about securing your business with the right firewall.
- Cloud Security: Securing data, applications, and infrastructure hosted in cloud environments (AWS, Azure, GCP). This is a booming field as more organizations migrate to the cloud. You’ll deal with identity and access management (IAM), data encryption in the cloud, and cloud compliance.
- Endpoint Security: Protecting individual devices like laptops, desktops, and mobile phones from threats. This involves antivirus software, endpoint detection and response (EDR), and mobile device management (MDM).
- Application Security (AppSec): Focuses on making software applications secure from design to deployment. You’ll learn about secure coding practices, penetration testing (pen testing) applications, and vulnerability management.
- Incident Response and Forensics: The “firefighters” of cybersecurity. When a breach occurs, incident responders investigate, contain, eradicate, and recover. Digital forensics involves gathering and analyzing evidence of cybercrimes. Learn about automated cybersecurity incident response.
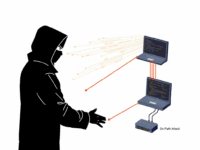
- Ethical Hacking/Penetration Testing: Legally simulating cyberattacks to find vulnerabilities before malicious actors do. This requires a deep understanding of attack techniques, tools, and methodologies. A popular certification in this area is CEH (Certified Ethical Hacker).
- Governance, Risk, and Compliance (GRC): Focuses on developing policies, managing risks, and ensuring an organization complies with regulations (e.g., GDPR, HIPAA, ISO 27001). This role often involves more policy and strategy than hands-on technical work but is absolutely critical. For example, understanding ISO 27001 certification is key here.
Intermediate Certifications for Your Cybersecurity Roadmap 2025
As you specialize, certain certifications become more relevant and valuable:
- (ISC)² SSCP (Systems Security Certified Practitioner): A good step up from Security+, covering more hands-on implementation and operational security.
- CompTIA CySA+ (Cybersecurity Analyst): Focuses on behavioral analytics to improve the overall state of IT security. It covers threat detection, vulnerability management, and incident response.
- EC-Council Certified Ethical Hacker (CEH): If ethical hacking is your path, CEH is widely recognized for demonstrating skills in penetration testing and offensive security.
- Vendor-Specific Certifications: Depending on your chosen specialization (e.g., cloud security), you might pursue certifications from AWS (e.g., AWS Certified Security – Specialty) or Microsoft Azure (e.g., Azure Security Engineer Associate).
- GIAC Certifications: These are highly respected, technically challenging, and often more expensive, but they offer deep specialization (e.g., GSEC for general security, GCIH for incident handling).
Choosing a specialization isn’t about limiting yourself; it’s about focusing your energy to become truly exceptional in a high-demand area.
The Power of Hands-On Experience: Building Your Skillset
Certifications are great, but practical experience is king. Employers want to see that you can do the work, not just know about it.
- Build a Homelab: Set up virtual machines with different operating systems, practice networking, configure firewalls, and experiment with security tools. This is a low-cost, high-impact way to learn.
- Participate in Capture The Flag (CTF) Events: These are cybersecurity competitions where you solve challenges related to ethical hacking, forensics, and more. Sites like Hack The Box, TryHackMe, and OverTheWire offer excellent practice.
- Internships and Entry-Level Roles: Nothing beats real-world experience. Look for internships, security analyst roles, or even IT support positions where you can gain exposure to security operations. This is often the most critical step in solidifying your cybersecurity career path.
- Open-Source Contributions: Contribute to open-source security projects. This showcases your skills and allows you to learn from experienced developers.
- Bug Bounty Programs: For those interested in offensive security, legally finding and reporting vulnerabilities in real-world applications through bug bounty platforms can be a thrilling and rewarding experience.
Becoming a Cybersecurity Professional: Advanced Roles and Leadership in 2025
You’ve built your foundation, gained intermediate skills, and perhaps even specialized. Now, your cybersecurity roadmap 2025 leads to advanced roles, leadership positions, and strategic influence. This stage is about mastering complex challenges and shaping the future of digital defense.
Advanced Roles and Senior Cybersecurity Career Path Opportunities
At this level, you’re not just executing tasks; you’re designing strategies, leading teams, and influencing organizational security posture.
- Security Architect: Designs and builds secure systems, networks, and applications. They translate business requirements into technical security solutions.
- Security Engineer (Senior/Lead): Implements, maintains, and troubleshoots complex security systems, often specializing in areas like cloud security, network security, or identity and access management.
- Incident Response Team Lead/Manager: Leads the charge during security incidents, coordinating response efforts, and managing forensic investigations.
- Penetration Testing Lead/Manager: Manages teams of ethical hackers, oversees red team exercises, and provides strategic insights into an organization’s security weaknesses.
- Security Operations Center (SOC) Manager: Oversees the 24/7 monitoring and analysis of security events, managing SOC analysts and processes.
- GRC Specialist/Manager: Develops and implements security policies, ensures compliance with regulations, and manages risk assessments at an organizational level.
- Application Security Engineer (Senior): Works closely with development teams to embed security throughout the software development lifecycle (SDLC).
- Cloud Security Architect/Engineer (Senior): Specializes in designing, implementing, and managing security controls within complex cloud environments. For further reading, check out a strong aerospace cybersecurity strategy, which highlights advanced implementation.
Leadership and Executive Roles: The Pinnacle of the Cybersecurity Career Path
The highest levels of the cybersecurity roadmap 2025 involve significant responsibility, strategic vision, and leadership.
- Chief Information Security Officer (CISO): The top security executive in an organization. Responsible for the overall cybersecurity strategy, risk management, and security posture. This role requires technical depth, business acumen, and strong leadership skills. The AI impact on the CISO role in 2025 is a significant consideration for aspiring CISOs.
- Director of Security/VP of Cybersecurity: Manages large security teams, develops departmental strategies, and reports to the CISO or other executive leadership.
- Security Consultant: Works with multiple organizations, providing expert advice on security strategy, architecture, and incident response. This role requires broad expertise and excellent communication skills.
Advanced Certifications and Continuous Learning
To reach and maintain professional status, advanced certifications are critical:
- CISSP (Certified Information Systems Security Professional): Widely regarded as the gold standard for experienced security professionals, covering eight domains of security. Requires 5 years of full-time security experience.
- CISM (Certified Information Security Manager): Focuses on information security management, governance, program development, and incident management. Ideal for those moving into management roles.
- CISA (Certified Information Systems Auditor): For professionals who audit, control, monitor, and assess an organization’s information technology and business systems.
- CRISC (Certified in Risk and Information Systems Control): Focuses on enterprise risk management and how it relates to information technology.
- CCSP (Certified Cloud Security Professional): Specializes in cloud security architecture, design, and operations.
- Offensive Security Certified Professional (OSCP): A highly respected, hands-on penetration testing certification for those seeking deep technical offensive skills.
Table: Advanced Certifications and Their Focus
| Certification | Focus Area | Target Audience | Prerequisites |
|---|---|---|---|
| CISSP | Comprehensive security management, architecture | Senior Security Professionals, Architects | 5 years exp. in 2+ domains |
| CISM | Info security governance, program management | Security Managers, Directors | 5 years exp. in InfoSec |
| CISA | IT audit, control, assurance | IT Auditors, Assurance Professionals | 5 years exp. in IT Audit |
| CRISC | Enterprise risk management, IS control | Risk Professionals, Project Managers | 3 years exp. in risk management |
| OSCP | Hands-on penetration testing, exploit development | Pen Testers, Ethical Hackers | Strong Linux, networking |
Continuous learning is non-negotiable. The threat landscape changes daily. Staying current means:
- Regularly reading industry publications: Like Cyber Tech Journals.
- Attending webinars and conferences: Stay updated on new threats and technologies.
- Participating in professional communities: Share knowledge and learn from peers.
- Pursuing micro-credentials and specialized courses: Focus on emerging areas like quantum security or AI in cybersecurity.
- Keeping up with the latest cyber threats 2024 and what to expect in 2025.
Emerging Trends and Future-Proofing Your Cybersecurity Roadmap 2025
The cybersecurity landscape is a constantly shifting battleground. To stay ahead and ensure your cybersecurity career path remains relevant and thriving, it’s crucial to understand the emerging trends shaping the industry in 2025 and beyond.
Key Trends Defining Cybersecurity in 2025
- AI and Machine Learning in Security: AI is a double-edged sword. It’s being used by attackers to create more sophisticated threats (e.g., deepfakes for phishing), but also by defenders for enhanced threat detection, behavioral analytics, and automated incident response. Understanding AI’s role in security, including AI threat detection tools that actually work, will be paramount.
- Zero Trust Architecture: The principle of “never trust, always verify” is becoming the default. Organizations are moving away from traditional perimeter-based security to verify every user, device, and application attempting to access resources, regardless of location.
- Cloud-Native Security: As cloud adoption accelerates, securing cloud-native applications, containers, and serverless functions will be a critical skill. This goes beyond basic cloud security to deep integration within cloud platforms.
- IoT and OT Security: The proliferation of Internet of Things (IoT) devices in homes and workplaces, and Operational Technology (OT) in industrial control systems, creates new attack surfaces. Securing these interconnected devices and critical infrastructure will be a growing demand. This includes understanding cybersecurity in industrial control systems.
- Quantum Cryptography: While still in its early stages, the eventual advent of quantum computers poses a threat to current encryption methods. Research and development in quantum-safe cryptography will gain momentum.
- Cyber Resilience: Beyond just prevention, organizations are focusing on their ability to withstand, respond to, and recover from cyberattacks quickly and effectively. This involves robust disaster recovery and business continuity planning. Learn how to prepare a disaster recovery plan for your business.
- Human-Centric Security (Cyber Hygiene): Recognizing that the human element is often the weakest link, emphasis on security awareness training, strong cyber hygiene in 2025, and phishing prevention will intensify.
Adapting Your Cybersecurity Roadmap 2025 for Future Success
To future-proof your career, consider these strategies:
- Embrace Lifelong Learning: The learning never stops. Dedicate time each week to study new technologies, threat intelligence, and attack techniques.
- Specialize in Emerging Areas: Look at areas like AI security, quantum cryptography, or advanced cloud security. These niches will see significant growth.
- Develop Soft Skills: Communication, problem-solving, critical thinking, and leadership are increasingly vital, especially as you move into management and executive roles.
- Stay Connected: Join professional organizations, attend industry events, and network with peers. This keeps you informed and opens doors to new opportunities.
Building Your Network and Personal Brand
As you progress along your cybersecurity roadmap 2025, technical skills are paramount, but they’re not the only ingredients for success. Building a strong professional network and cultivating a personal brand are equally crucial for advancing your cybersecurity career path.
The Importance of Networking
Networking isn’t just about finding a job; it’s about connecting with peers, mentors, and industry leaders who can offer advice, share insights, and collaborate on projects.
- Join Professional Organizations: Associations like ISACA, (ISC)², and local OWASP chapters offer invaluable opportunities for learning and networking. They often host events, webinars, and conferences.
- Attend Conferences and Meetups: Industry conferences (e.g., RSA Conference, Black Hat, DEF CON) are excellent for hearing about the latest trends, meeting experts, and discovering new technologies. Local meetups provide a more intimate setting for connecting with your community.
- Engage Online: LinkedIn, Twitter, and specialized forums are great places to connect. Follow thought leaders, participate in discussions, and share relevant content.
- Seek Mentors: Find experienced professionals who are willing to guide you. A mentor can offer career advice, introduce you to their network, and provide insights you wouldn’t get otherwise. Conversely, consider becoming a mentor yourself as you gain experience – it’s a great way to solidify your own knowledge and give back to the community.
Cultivating Your Personal Brand in Cybersecurity
Your personal brand is how you present yourself to the world – your unique combination of skills, experience, and personality. A strong personal brand can open doors, establish credibility, and differentiate you in a competitive market.
Create a Professional Online Presence:
- LinkedIn: Optimize your profile with relevant keywords, showcase your skills and certifications, and actively engage with industry content. Think of it as your digital resume and professional networking hub.
- Personal Website/Blog: A personal website or blog allows you to demonstrate your expertise by writing about cybersecurity topics, sharing project insights, or documenting your learning journey.
Contribute and Share Knowledge:
- Open Source Projects: Contribute to open-source cybersecurity tools or projects. This demonstrates your practical skills and ability to collaborate.
- Write Articles/Blog Posts: Share your knowledge by writing articles for platforms like Cyber Tech Journals or your own blog. This establishes you as a thought leader.
- Speak at Events: As you gain expertise, consider speaking at local meetups, webinars, or even smaller conferences. Public speaking enhances your visibility and credibility.
Be a Continuous Learner and Adaptable:
- Demonstrate your commitment to learning by sharing new certifications, course completions, or insights from recent industry reports. This shows you’re proactive and dedicated to staying current in your cybersecurity roadmap 2025.
- Highlight your ability to adapt to new technologies and threats. The cybersecurity field is dynamic, and adaptability is a highly valued trait.
“Your network is your net worth in the professional world. Nurture it, and it will propel your cybersecurity career path forward.”
By actively networking and intentionally building your personal brand, you’re not just waiting for opportunities; you’re creating them. You’re becoming a visible, trusted, and valuable member of the cybersecurity community.
Bottom Line : Chose your path wisely
Navigating the cybersecurity roadmap 2025 from a complete beginner to a seasoned professional is an exciting, challenging, and incredibly rewarding journey. We’ve explored the essential foundational skills, the critical role of certifications, the diverse specializations available, and the importance of hands-on experience. We’ve also highlighted the emerging trends that will shape the industry and emphasized the invaluable contribution of networking and personal branding to your cybersecurity career path.
Remember, the world of cybersecurity is dynamic. What’s cutting-edge today might be standard practice tomorrow, and new threats are always on the horizon. This means that a commitment to continuous learning isn’t just a recommendation; it’s a necessity. Embrace curiosity, maintain a proactive mindset, and always be ready to adapt.
Actionable Next Steps:
- Assess Your Current Skills: Honestly evaluate where you stand in terms of core IT knowledge (networking, OS, scripting). Identify gaps.
- Start Your Foundational Learning: Dive into resources for CompTIA A+, Network+, or Security+. Online courses, books, and free tutorials abound.
- Build Your Homelab: Get your hands dirty! Set up virtual machines, experiment with tools, and break things (then fix them!).
- Target Your First Certification: Aim for CompTIA Security+ or (ISC)² CC to validate your entry-level knowledge.
- Explore Specializations: Research the different cybersecurity domains. Which one sparks your interest the most? Look into more specific roles on career paths in cyber security.
- Network Actively: Connect with other professionals on LinkedIn, join local meetups, and seek out mentors.
- Stay Informed: Follow reputable cybersecurity news sources, blogs, and podcasts (like Cyber Tech Journals) to keep abreast of the latest developments in 2025.
The demand for skilled cybersecurity professionals is soaring, and this trend is only set to continue. Your journey will require dedication and perseverance, but the impact you can make in protecting individuals, businesses, and critical infrastructure is immeasurable. Take that first step today, and embark on a fulfilling and impactful cybersecurity career path in 2025!














Leave a comment