In an increasingly interconnected and threat-laden digital landscape, the bedrock of any robust cybersecurity strategy for businesses, irrespective of their size, remains a powerful firewall. As we navigate 2025, the stakes have never been higher, with cyber attackers evolving their tactics at an alarming rate. Businesses today face everything from sophisticated ransomware and phishing attacks to advanced persistent threats, making the selection of the best business firewalls 2025 a critical strategic decision. This comprehensive guide will delve into the essential business firewall solutions, explore the capabilities of next generation firewall (NGFW) 2025 technology, and help you understand what constitutes the best firewall for small business 2025 versus more expansive enterprise firewall solutions. We’ll also dissect the nuances of firewall for business networks, the growing appeal of managed firewall services 2025, and the rise of cloud-ready firewall for business deployments, offering a definitive firewall buying guide 2025 and a crucial business firewall comparison to future-proof your organization’s security posture.
Table of Contents
Key Takeaways
- Evolving Threat Landscape: Traditional firewalls are no longer sufficient against 2025’s sophisticated cyber threats. Next Generation Firewalls (NGFWs) are essential for deep packet inspection, application control, and integrated threat intelligence.
- Tailored Solutions for All Businesses: The “best” firewall depends on your specific business size, budget, and security needs. Small businesses benefit from user-friendly, cost-effective options, while enterprises require scalable, feature-rich solutions.
- Cloud and Managed Services are Key: Cloud-ready firewalls offer flexibility and scalability for modern, distributed workforces. Managed firewall services provide expert 24/7 monitoring and response, alleviating the burden on internal IT teams.
- Beyond Basic Protection: Future-proofing means selecting firewalls with AI/ML integration, zero-trust capabilities, and advanced threat prevention (ATP) features to combat evolving and unknown threats.
- Strategic Investment, Not Just an Expense: A robust firewall in 2025 is a critical investment that protects data, ensures business continuity, and maintains customer trust, requiring careful evaluation using a comprehensive buying guide.
Evolving Role of Best Business Firewalls
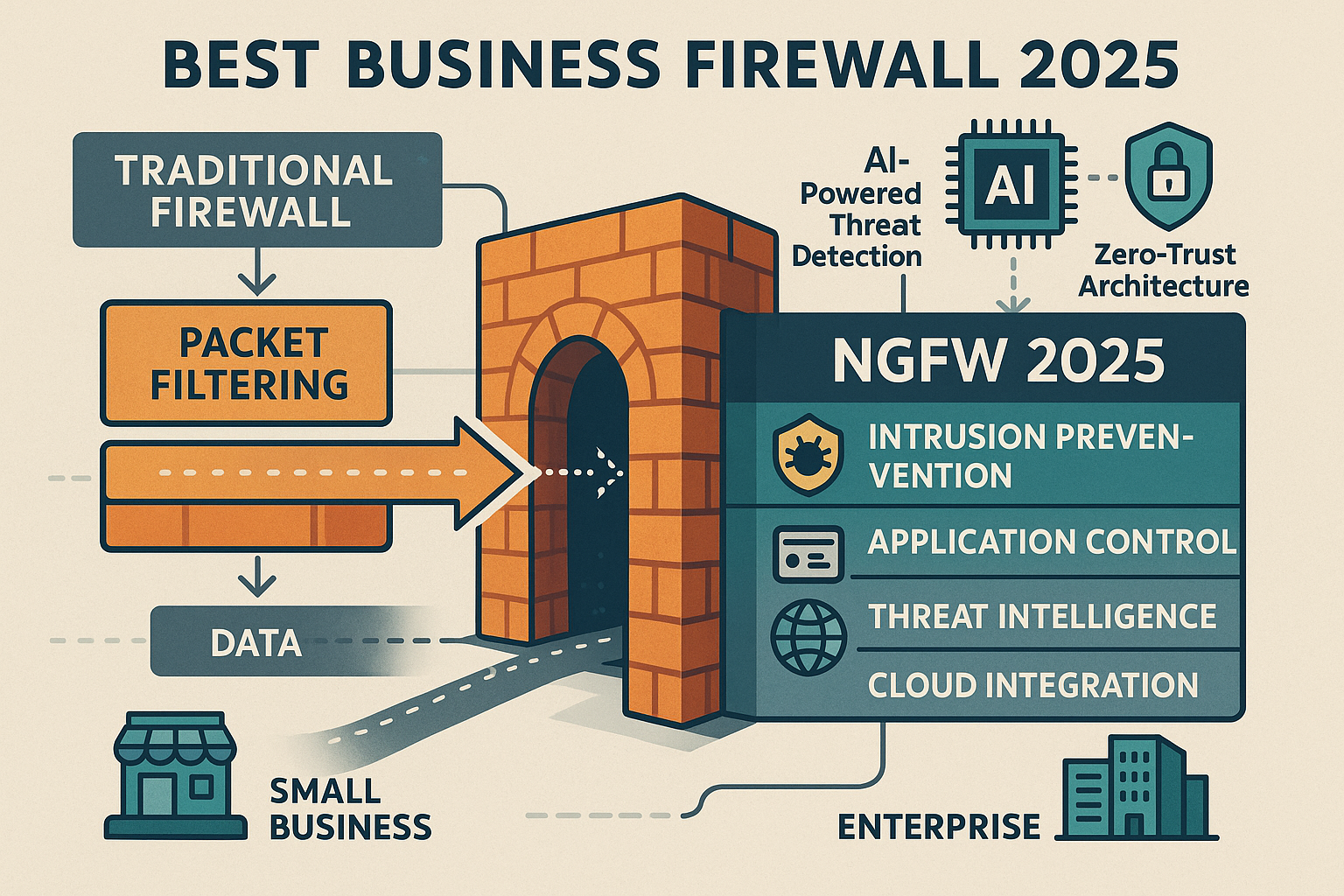
The concept of a firewall has been around for decades, acting as the primary gatekeeper between a private internal network and the wild west of the internet. Initially, firewalls performed basic packet filtering, allowing or denying traffic based on simple rules like IP addresses and port numbers. However, the digital world of 2025 is a vastly different place. Cyber threats have become incredibly sophisticated, stealthy, and persistent, rendering legacy firewalls largely inadequate.
Today, business firewall solutions are dynamic, intelligent, and multi-layered security platforms. They are no longer just blocking unwanted connections; they are actively inspecting traffic, identifying malicious patterns, controlling application usage, and integrating with broader security ecosystems. The move towards remote work, cloud computing, and the proliferation of IoT devices has further complicated network perimeters, demanding more agile and adaptable firewall technologies.
The Rise of Next Generation Firewall (NGFW) 2025
For businesses serious about their security in 2025, the discussion invariably centers around the next generation firewall (NGFW) 2025. What exactly makes a firewall “next generation”? It’s a combination of traditional firewall capabilities with advanced features designed to provide deeper inspection, broader context, and more proactive threat prevention.
Key capabilities of an NGFW include:
- Deep Packet Inspection (DPI): Unlike traditional firewalls that only look at header information, NGFWs examine the actual data payload of network packets. This allows them to identify and block threats embedded within legitimate-looking traffic.
- Application Awareness and Control: NGFWs can identify and control applications regardless of the port or protocol they use. This means businesses can enforce policies like blocking social media access during work hours or prioritizing business-critical applications.
- Intrusion Prevention System (IPS): An integrated IPS actively monitors network traffic for known attack signatures and anomalies, automatically blocking malicious attempts before they can infiltrate the network.
- Integrated Threat Intelligence: NGFWs leverage global threat intelligence feeds, constantly updating their knowledge of new and emerging threats, zero-day exploits, and malicious IPs. This proactive defense mechanism is crucial for future-proofing security.
- Identity Awareness: They can integrate with directory services (like Active Directory) to apply security policies based on individual users or groups, rather than just IP addresses.
- VPN Capabilities: Securely connect remote workers and branch offices to the main network.
- SSL/TLS Decryption: Inspect encrypted traffic for hidden threats, a critical feature as more web traffic becomes encrypted.
- Sandboxing: Isolate suspicious files in a safe environment to observe their behavior before they can impact the live network.
The shift to an NGFW is not merely an upgrade; it’s a fundamental change in how businesses approach network security, offering a significantly enhanced defense against the complex threat landscape of 2025. For more insights into bolstering your overall digital defenses, consider exploring 10 Strategies to Strengthen Digital Security.
Best Firewall for Small Business 2025: Tailored Security
Small businesses often operate with limited IT budgets and staff, yet they are increasingly targeted by cybercriminals who perceive them as easier prey than larger enterprises. Therefore, finding the best firewall for small business 2025 involves a balance of robust security features, ease of management, and cost-effectiveness.
For small businesses, simplicity doesn’t mean sacrificing essential protection. The ideal firewall solution should offer:
- Ease of Deployment and Management: Solutions with intuitive interfaces and straightforward configuration are paramount. Many small businesses don’t have dedicated cybersecurity experts.
- Comprehensive Threat Protection: Even small businesses need protection against ransomware, phishing, malware, and intrusion attempts. Look for integrated antivirus, IPS, and web filtering.
- VPN for Remote Access: With hybrid and remote work becoming standard, secure VPN capabilities are non-negotiable for employees connecting from various locations.
- Scalability (Future Growth): While focusing on current needs, consider solutions that can scale as your business grows, adding more users or features without a complete overhaul.
- Affordable Pricing: Both upfront costs and ongoing licensing/subscription fees need to fit within a small business budget.
- Reliable Vendor Support: Access to responsive technical support is crucial when issues arise.
Recommended Firewall Options for Small Businesses in 2025:
- Fortinet FortiGate (Entry-Level Models):
- Pros: Excellent security features, integrated NGFW capabilities, strong threat intelligence, good value for money, scalable.
- Cons: Can have a steeper learning curve for advanced features.
- Why it’s good: FortiGate offers enterprise-grade security scaled down for smaller environments. Their entry-level models (e.g., FortiGate 40F, 60F) provide a powerful security fabric.
- Sophos XGS Series (Small Business Editions):
- Pros: User-friendly interface, strong synchronized security (Endpoint and Firewall work together), good threat protection, excellent reporting.
- Cons: Synchronized security benefits require Sophos endpoints.
- Why it’s good: Sophos is renowned for its ease of use and integrated approach, making it ideal for small businesses seeking comprehensive protection without complexity.
- Ubiquiti UniFi Dream Machine (UDM/UDM Pro):
- Pros: All-in-one networking device (router, switch, access point, firewall), highly affordable, great for managing entire UniFi ecosystem, good basic firewall features.
- Cons: Not a full NGFW; advanced security features are less comprehensive than dedicated firewalls.
- Why it’s good: Perfect for micro-businesses or those already invested in the UniFi ecosystem, offering centralized management and solid foundational security.
- WatchGuard Firebox T Series:
- Pros: Strong security, comprehensive NGFW features, easy-to-use cloud management, good for distributed small offices.
- Cons: Licensing can add up for full feature sets.
- Why it’s good: WatchGuard offers robust security with a focus on ease of deployment and management, fitting well into small business environments.
Choosing the right solution often involves a trade-off between features, complexity, and price. A small business must identify its core needs and select a firewall that meets them efficiently without overspending on unnecessary functionalities. Understanding if you are securing your business with the right firewall is a crucial first step.
Enterprise Firewall Solutions and Firewall for Business Networks
When we talk about enterprise firewall solutions and firewall for business networks in larger organizations, the requirements become far more extensive and complex. Enterprises deal with vast amounts of data, numerous endpoints, diverse applications, strict regulatory compliance, and a higher profile that makes them prime targets for sophisticated cyberattacks.
Enterprise-grade firewalls must offer:
- High Performance and Throughput: Capable of handling massive traffic volumes without performance degradation, especially with encrypted traffic inspection.
- Advanced Threat Prevention (ATP): Beyond basic IPS, including sandboxing, anti-malware, anti-bot, and advanced persistent threat (APT) protection.
- Centralized Management: The ability to manage multiple firewalls across various locations (data centers, branch offices, cloud environments) from a single console.
- Granular Policy Control: Highly detailed control over user, application, and content access, essential for implementing a zero-trust architecture.
- Scalability and Redundancy: Solutions that can scale horizontally and vertically, with high availability and redundancy features to ensure continuous operation.
- Integration with Security Ecosystems: Seamless integration with Security Information and Event Management (SIEM) systems, Endpoint Detection and Response (EDR) platforms, and other security tools.
- Cloud Integration: Support for hybrid and multi-cloud environments, extending security policies to cloud workloads.
- Deep Visibility and Reporting: Comprehensive logging, analytics, and reporting capabilities for compliance, auditing, and proactive threat hunting.
Leading Enterprise Firewall Solutions in 2025:
- Palo Alto Networks (PA Series):
- Pros: Industry leader in NGFW capabilities, excellent application identification (App-ID), highly effective threat prevention, strong cloud integration (Prisma Access).
- Cons: Premium pricing, can be complex to manage without dedicated expertise.
- Why it’s good: Palo Alto is often considered the gold standard for enterprises requiring top-tier security and advanced threat intelligence, offering unparalleled visibility and control.
- Cisco Secure Firewall (formerly Firepower):
- Pros: Deep integration with Cisco’s extensive networking and security portfolio, robust IPS/IDS, strong threat intelligence (Talos), good for existing Cisco environments.
- Cons: Can be resource-intensive, complexity in management for non-Cisco shops.
- Why it’s good: Leverages Cisco’s vast security research and global presence, ideal for enterprises already invested in Cisco infrastructure seeking unified security management.
- Check Point Quantum Security Gateways:
- Pros: Pioneer in firewall technology, comprehensive layered security (Threat Prevention, SandBlast Zero-Day Protection), unified management, good for highly regulated industries.
- Cons: Performance can be impacted with all blades enabled, licensing model can be complex.
- Why it’s good: Check Point offers a modular approach to security, allowing enterprises to customize their defense layers, excelling in advanced threat prevention and compliance.
- Fortinet FortiGate (High-End Models):
- Pros: High performance, broad security fabric integration, cost-effective for the feature set, robust SD-WAN capabilities.
- Cons: Management can be daunting for very large, distributed deployments without automation.
- Why it’s good: Fortinet offers a scalable and performant solution that extends from small businesses to large enterprises, with a strong focus on integrated security and operational efficiency.
For enterprises, selecting a firewall is part of a larger security architecture decision. It’s about how the firewall integrates with other security tools, how it supports a zero-trust model, and how it can adapt to the organization’s evolving digital footprint. Staying ahead of threats also requires understanding broader cybersecurity for businesses.
Managed Firewall Services 2025: Outsourcing Your Perimeter Security
For many businesses, particularly small to medium-sized enterprises (SMEs) and even some larger organizations, the complexity of managing a state-of-the-art firewall can be overwhelming. This is where managed firewall services 2025 come into play, offering a compelling alternative to in-house management.
Managed firewall services involve outsourcing the entire lifecycle of your firewall security to a third-party expert. This typically includes:
- Deployment and Configuration: Initial setup and customization of firewall rules and policies tailored to your business needs.
- 24/7 Monitoring: Constant surveillance for suspicious activities, alerts, and potential breaches.
- Threat Intelligence Updates: Regular updates to threat databases and signatures to protect against new vulnerabilities.
- Policy Management: Ongoing adjustments to firewall rules as your business needs or the threat landscape changes.
- Incident Response: Immediate action and mitigation in the event of a security incident.
- Reporting and Compliance: Regular reports on security posture, traffic analysis, and assistance with compliance requirements.
- Hardware/Software Maintenance: Keeping the firewall hardware and software up-to-date and patched.
Benefits of Managed Firewall Services:
- Access to Expertise: You gain access to a team of cybersecurity specialists without the cost of hiring them in-house.
- 24/7 Protection: Threats don’t sleep, and neither do managed service providers (MSPs). Your network is continuously monitored.
- Reduced Operational Burden: Frees up your internal IT staff to focus on core business initiatives, reducing workload and stress.
- Cost-Effectiveness: Often more predictable and potentially lower than maintaining an in-house security team, including training, tools, and staffing.
- Proactive Security: MSPs are often at the forefront of threat intelligence, implementing protections before new threats become widespread.
- Compliance Assistance: Many MSPs can help businesses meet regulatory compliance standards related to network security.
When to Consider Managed Firewall Services:
- Limited IT Staff/Expertise: If your team lacks the specialized skills or time to manage complex security solutions.
- Budget Constraints: When the cost of a full-time cybersecurity analyst is prohibitive.
- Need for 24/7 Coverage: If your business operates globally or requires round-the-clock protection.
- Rapid Growth: As your network expands, a managed service can scale more easily.
- Focus on Core Business: When you want to offload security management to focus on what you do best.
Choosing a reputable MSP is crucial. Look for providers with strong SLAs (Service Level Agreements), certifications, and a proven track record. For businesses seeking robust industrial control system protection, managed services can be an extension of a strong ICS cyber resilience strategy.
Cloud-Ready Firewall for Business: Securing the Distributed Enterprise
The shift to cloud computing, hybrid work models, and a distributed workforce means that traditional perimeter-based firewalls are no longer sufficient. Businesses need security that follows their data and users wherever they are. This is precisely the role of a cloud-ready firewall for business.
A cloud-ready firewall extends network security policies and enforcement to cloud environments, remote users, and branch offices, often delivered as a service (Firewall-as-a-Service, FWaaS). It provides centralized visibility and control over traffic flowing to and from cloud applications, SaaS platforms, and remote endpoints.
Key Characteristics of Cloud-Ready Firewalls:
- Global Reach: Enforces consistent security policies across all locations, including headquarters, branch offices, and remote users.
- Scalability: Easily scales up or down to meet changing business demands without hardware limitations.
- Flexibility: Supports various deployment models: virtual appliances in IaaS clouds (AWS, Azure, GCP), FWaaS, or hybrid approaches.
- Unified Policy Management: Allows IT teams to manage security policies for both on-premises and cloud resources from a single console.
- Secure Access Service Edge (SASE) Integration: Often a core component of SASE architectures, combining network security functions (FWaaS, CASB, SWG) with WAN capabilities into a single, cloud-native service.
- API Integration: Seamlessly integrates with cloud provider APIs for automated provisioning and policy enforcement.
- Threat Protection: Delivers the same advanced threat prevention capabilities as on-premises NGFWs, including IPS, anti-malware, and URL filtering, to cloud traffic.
Why Businesses Need Cloud-Ready Firewalls in 2025:
- Protecting Cloud Workloads: Ensures that applications and data hosted in public or private clouds are secured against unauthorized access and threats.
- Securing Remote Workers: Provides consistent security for employees working from home or on the go, often through a secure access client that directs their traffic through the cloud firewall.
- Streamlining Branch Office Connectivity: Replaces traditional hardware in branch offices with cloud-delivered security, simplifying management and reducing costs.
- Enabling Digital Transformation: Facilitates the secure adoption of new cloud technologies and SaaS applications.
- Enhancing Visibility: Offers a unified view of security events across the entire distributed network, simplifying compliance and auditing.
Leading vendors like Zscaler, Fortinet, Palo Alto Networks, and Cisco offer robust cloud-ready firewall solutions that are critical for modern businesses navigating the complexities of cloud adoption and hybrid work. For further reading on securing cloud environments, refer to Cloud Security Best Practices.
Firewall Buying Guide 2025: Making the Right Choice
Selecting the best business firewall 2025 is a significant investment that requires careful consideration. This firewall buying guide 2025 outlines the key factors to evaluate to ensure you choose a solution that aligns with your specific needs and future-proofs your security.
1. Assess Your Business Size and Needs:
- Small Business/SMB: Prioritize ease of use, integrated all-in-one features, and strong basic threat protection. Look for affordable options with good vendor support.
- Medium Business: Requires more scalability, advanced NGFW features (DPI, IPS, application control), centralized management for growing networks, and possibly some cloud integration.
- Enterprise: Demands high performance, comprehensive ATP, extensive reporting, deep integration with existing security ecosystems, and robust cloud capabilities.
2. Identify Your Specific Security Requirements:
- Threat Prevention: Do you need basic packet filtering, or advanced features like sandboxing, AI/ML-driven threat detection, and zero-day exploit protection?
- Application Control: Is it critical to manage which applications users can access and how?
- User/Identity-Based Policies: Do you need to apply different security rules based on individual users or groups?
- VPN Requirements: How many remote users need secure access? Do you have multiple branch offices?
- Web Content Filtering: Is controlling access to inappropriate or unproductive websites important?
- Email Security: Do you need integrated spam and phishing protection?
- Compliance: Are there specific industry regulations (HIPAA, GDPR, PCI DSS) that your firewall must help you meet?
3. Consider Your Network Architecture:
- On-Premises vs. Cloud vs. Hybrid: Do you need a physical appliance, a virtual firewall, or a cloud-delivered FWaaS solution? Many businesses will need a hybrid approach.
- Number of Locations: A single office versus multiple branches requires different management and deployment strategies.
- Expected Traffic Volume: High traffic and high numbers of concurrent users will demand higher throughput firewalls.
- Existing Infrastructure: How well will the new firewall integrate with your current network devices, servers, and security tools (e.g., SIEM, EDR)?
4. Evaluate Key Firewall Features:
- NGFW Capabilities: Ensure it has DPI, IPS, application control, and integrated threat intelligence.
- Performance: Check throughput rates for various traffic types (e.g., firewall, IPS, VPN, encrypted traffic). Don’t just look at advertised numbers; consider real-world scenarios.
- Management: Look for intuitive interfaces, centralized management for multiple devices, and automation capabilities.
- Reporting and Analytics: Comprehensive dashboards, logs, and customizable reports are essential for visibility and compliance.
- Scalability: Can the solution grow with your business? Can it handle increased users, traffic, or new services?
- Redundancy and High Availability: Essential for business continuity to ensure the firewall doesn’t become a single point of failure.
5. Vendor Reputation and Support:
- Customer Reviews and Analyst Reports: Consult independent reviews (Gartner, Forrester) and peer feedback.
- Technical Support: Evaluate the vendor’s support options (24/7, phone, email, chat), response times, and knowledge base.
- Updates and Patches: How frequently does the vendor release security updates and patches?
6. Cost Analysis:
- Initial Hardware/Software Cost: The upfront purchase price.
- Licensing Fees: Annual subscriptions for threat intelligence, support, and advanced features.
- Maintenance: Costs for hardware maintenance or replacements.
- Deployment and Configuration: Internal labor or external consultant costs.
- Training: For your IT staff to manage the new system.
- Managed Services: If you opt for outsourcing, factor in the ongoing service fees.
By systematically working through these considerations, you can create a comprehensive business firewall comparison and choose a solution that provides optimal security for your organization in 2025 and beyond.
Business Firewall Comparison: Top Contenders in 2025
To help you make an informed decision, let’s look at a business firewall comparison of some of the leading solutions for 2025, categorizing them by their typical target audience and strengths.
| Feature/Vendor | Best For | Key Strengths | Considerations |
|---|---|---|---|
| Fortinet FortiGate | Small to Enterprise (Scalable) | Comprehensive security fabric, strong NGFW, SD-WAN, unified management, good performance/cost ratio. | Can be complex for small businesses without simplified management options. |
| Sophos XGS Series | Small to Medium Business | User-friendly interface, “Synchronized Security” (endpoint & firewall), excellent reporting, easy deployment. | Best value when paired with Sophos endpoint protection. |
| Palo Alto Networks PA | Enterprise, Cloud-Centric | Industry-leading NGFW, App-ID, superior threat prevention, robust cloud integration (Prisma Access). | Premium pricing, often requires specialized expertise for full optimization. |
| Cisco Secure Firewall | Enterprise (Cisco Ecosystem) | Deep integration with Cisco infrastructure, advanced IPS/IDS (Talos), comprehensive endpoint integration. | Can be resource-intensive and more complex for non-Cisco environments. |
| Check Point Quantum | Enterprise, High Security | Modular “Software Blades” for granular control, strong zero-day protection, compliance focus. | Performance can degrade with many blades active, licensing can be intricate. |
| Ubiquiti UniFi UDM/Pro | Micro/Small Business (DIY) | Affordable, all-in-one networking & security, simple management for UniFi users, aesthetic design. | Not a full NGFW, less advanced threat protection than dedicated firewalls. |
| WatchGuard Firebox | Small to Medium Business | Strong security features, cloud-based management, good for distributed environments. | Licensing costs can increase for full feature sets. |
| Zscaler (FWaaS) | Cloud-First, Distributed Work | Cloud-native, zero-trust network access (ZTNA), SASE architecture, secure web gateway (SWG), scale. | Primarily a cloud-delivered service, may require a hybrid approach for on-premise components. |
This table provides a high-level overview. The “best” choice will always depend on your specific environment, budget, and risk tolerance. It’s highly recommended to get demos and conduct proofs-of-concept (POCs) with shortlisted vendors before making a final decision. For businesses looking for general advice on protecting their digital assets, a guide on cybersecurity for small businesses can be very helpful.
Conclusion: Future-Proofing Your Business with the Right Firewall in 2025
As we’ve explored, the landscape of cybersecurity in 2025 demands more than just a basic barrier. The best business firewall 2025 is an intelligent, adaptable, and multi-layered security platform that serves as the cornerstone of your organization’s digital defense. Whether you’re a small business needing intuitive, integrated protection or a large enterprise requiring high-performance, feature-rich NGFW 2025 capabilities, the market offers a diverse range of business firewall solutions to meet your specific needs.
Investing in a robust firewall is not merely an IT expenditure; it’s a strategic investment in business continuity, data integrity, and customer trust. The rise of managed firewall services 2025 and cloud-ready firewall for business deployments underscores the industry’s shift towards more flexible, scalable, and expert-driven security.
By utilizing a comprehensive firewall buying guide 2025, understanding the nuances of enterprise firewall solutions versus the best firewall for small business 2025, and performing a thorough business firewall comparison, you can ensure your firewall for business networks is truly future-proof. Don’t let your firewall become a relic of the past; empower your business with the cutting-edge security it needs to thrive in 2025 and beyond.
Actionable Next Steps:
- Assess Your Current Firewall: Understand its capabilities and limitations against the threats of 2025. Is it an NGFW? Does it support cloud integration?
- Define Your Security Requirements: Map out your specific needs regarding threat prevention, application control, remote access, and compliance.
- Evaluate Your Resources: Determine if your internal IT team has the expertise and bandwidth to manage a modern firewall, or if managed firewall services 2025 are a better fit.
- Research Top Vendors: Look into the leaders in the space (Fortinet, Palo Alto, Sophos, Cisco, Check Point) and shortlist options that align with your budget and requirements.
- Request Demos and POCs: Experience the solutions firsthand. Test them in your environment to see how they perform and integrate.
- Plan for Scalability and Integration: Choose a solution that can grow with your business and integrate seamlessly with your broader security ecosystem.
By taking these steps, you’ll be well-equipped to select a firewall that not only protects your business today but also adapts to the evolving cyber threats of tomorrow.











It’s really a nice and helpful piece of information. I am satisfied that you just shared this useful information with us.
Please stay us informed like this. Thank you for sharing.
Excellent items from you, man. I’ve be mindful your stuff previous to and you are just extremely magnificent.
I really like what you’ve received here, certainly like what you’re saying and the best way in which
you are saying it. You’re making it entertaining and you still take care of to keep it smart.
I cant wait to read much more from you. This is really a wonderful site.