How-To
Find practical how-to guides for cybersecurity tasks like setting up firewalls, checking compliances, securing cloud environments, and more. Follow simple steps to implement best practices, solve common issues, and strengthen your defenses with confidence.
How to Respond to an ICS Cybersecurity Breach: Readiness & Recovery Guide
Industrial Control Systems (ICS) face growing cyber threats, and a breach can disrupt critical operations. This guide explains how to prepare, respond, and...
ByKumar SNovember 27, 2025Shadow AI Detection: How to Identify Unauthorized AI Tools in Your Organization
Picture this scenario: Your data loss prevention system alerts you to a massive data breach. After investigation, you discover an employee uploaded sensitive...
ByCyberTech JournalsSeptember 8, 2025How to Encrypt Sensitive Files Before Sharing Them: Complete 2025 Security Guide
Did you know that the average cost of a data breach reached an all-time high in 2024 of $4.88 million, representing a 10%...
ByKumar SJuly 11, 2025The Essential Guide to Vulnerability Patch Management and Hardening
A staggering 60% of data breaches in 2025 involved vulnerabilities for which patches were available but not applied! This alarming statistic from the...
ByKumar SJuly 9, 2025How to Send Secure Email in Outlook: A Step-by-Step Guide
In today’s digital age, ensuring the security of your emails is more important than ever. Whether you’re sharing sensitive business information, personal data,...
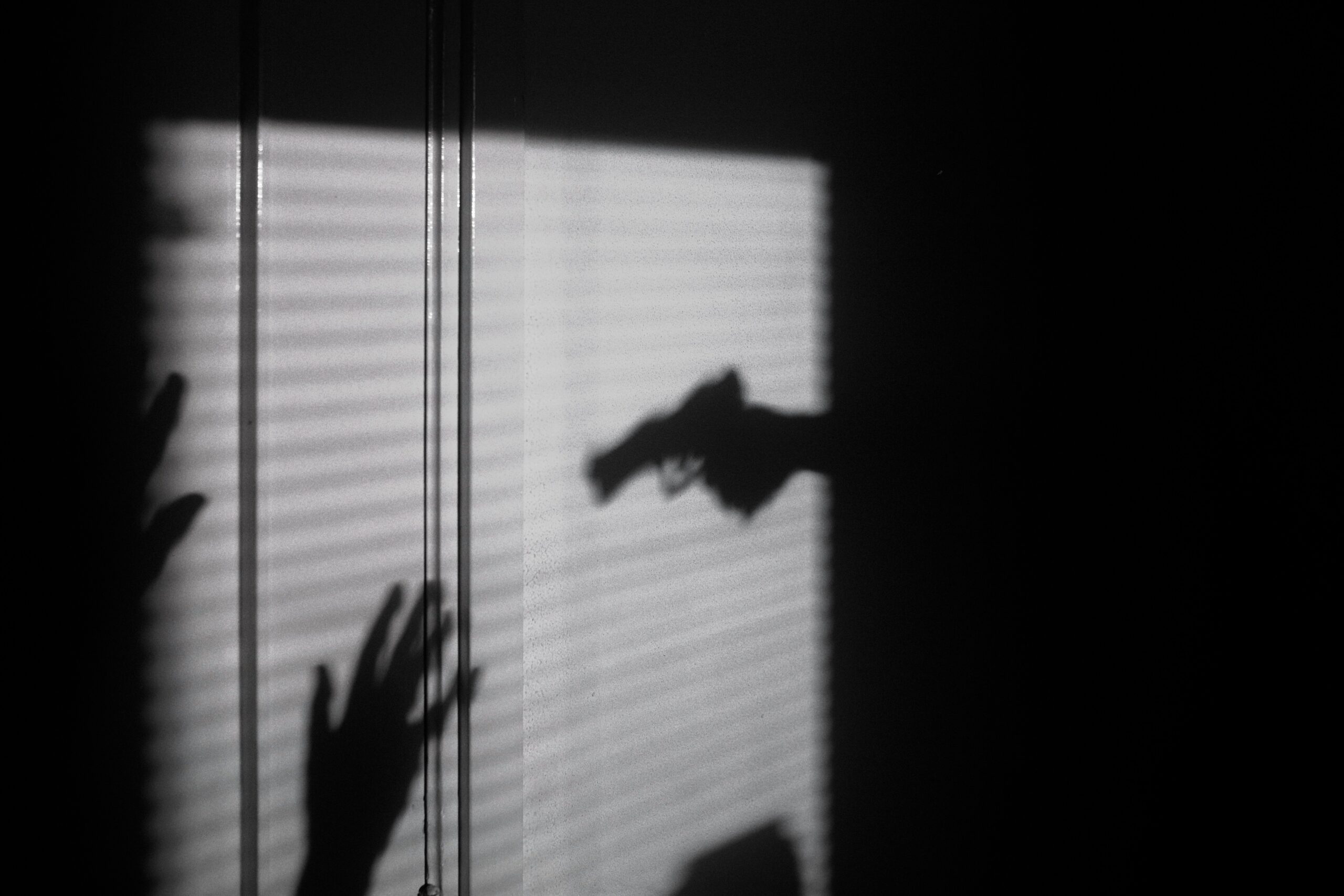
ByKumar SApril 25, 2025How to Remove Ransomware: A Practical and Comprehensive Recovery Guide
The digital landscape is a battlefield, and ransomware is one of the most devastating weapons in a cybercriminal’s arsenal. Imagine logging into your...
ByKumar SApril 23, 2025How to Train Employees on Cybersecurity Awareness & Prevent Human Errors
In today’s digital landscape, train employees on cybersecurity is no longer optional—it’s essential. As cybercriminals increasingly target human vulnerabilities through phishing, social engineering,...
ByKumar SApril 1, 2025How to Conduct a Cyber Risk Assessment for Your Business
Here’s a shocking reality: 60% of small businesses close within six months of experiencing a cyber attack. Yet, according to recent studies, only...
ByKumar SMarch 25, 2025